Wannacry Is Ransomware That Contains a Worm What If a System Cannot (Currently) Component
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-

North Korean Cyber Capabilities: in Brief
North Korean Cyber Capabilities: In Brief Emma Chanlett-Avery Specialist in Asian Affairs Liana W. Rosen Specialist in International Crime and Narcotics John W. Rollins Specialist in Terrorism and National Security Catherine A. Theohary Specialist in National Security Policy, Cyber and Information Operations August 3, 2017 Congressional Research Service 7-5700 www.crs.gov R44912 North Korean Cyber Capabilities: In Brief Overview As North Korea has accelerated its missile and nuclear programs in spite of international sanctions, Congress and the Trump Administration have elevated North Korea to a top U.S. foreign policy priority. Legislation such as the North Korea Sanctions and Policy Enhancement Act of 2016 (P.L. 114-122) and international sanctions imposed by the United Nations Security Council have focused on North Korea’s WMD and ballistic missile programs and human rights abuses. According to some experts, another threat is emerging from North Korea: an ambitious and well-resourced cyber program. North Korea’s cyberattacks have the potential not only to disrupt international commerce, but to direct resources to its clandestine weapons and delivery system programs, potentially enhancing its ability to evade international sanctions. As Congress addresses the multitude of threats emanating from North Korea, it may need to consider responses to the cyber aspect of North Korea’s repertoire. This would likely involve multiple committees, some of which operate in a classified setting. This report will provide a brief summary of what unclassified open-source reporting has revealed about the secretive program, introduce four case studies in which North Korean operators are suspected of having perpetrated malicious operations, and provide an overview of the international finance messaging service that these hackers may be exploiting. -

Adaptive Android Kernel Live Patching
Adaptive Android Kernel Live Patching Yue Chen Yulong Zhang Zhi Wang Liangzhao Xia Florida State University Baidu X-Lab Florida State University Baidu X-Lab Chenfu Bao Tao Wei Baidu X-Lab Baidu X-Lab Abstract apps contain sensitive personal data, such as bank ac- counts, mobile payments, private messages, and social Android kernel vulnerabilities pose a serious threat to network data. Even TrustZone, widely used as the se- user security and privacy. They allow attackers to take cure keystore and digital rights management in Android, full control over victim devices, install malicious and un- is under serious threat since the compromised kernel en- wanted apps, and maintain persistent control. Unfortu- ables the attacker to inject malicious payloads into Trust- nately, most Android devices are never timely updated Zone [42, 43]. Therefore, Android kernel vulnerabilities to protect their users from kernel exploits. Recent An- pose a serious threat to user privacy and security. droid malware even has built-in kernel exploits to take Tremendous efforts have been put into finding (and ex- advantage of this large window of vulnerability. An ef- ploiting) Android kernel vulnerabilities by both white- fective solution to this problem must be adaptable to lots hat and black-hat researchers, as evidenced by the sig- of (out-of-date) devices, quickly deployable, and secure nificant increase of kernel vulnerabilities disclosed in from misuse. However, the fragmented Android ecosys- Android Security Bulletin [3] in recent years. In ad- tem makes this a complex and challenging task. dition, many kernel vulnerabilities/exploits are publicly To address that, we systematically studied 1;139 An- available but never reported to Google or the vendors, droid kernels and all the recent critical Android ker- let alone patched (e.g., exploits in Android rooting nel vulnerabilities. -

2015 Threat Report Provides a Comprehensive Overview of the Cyber Threat Landscape Facing Both Companies and Individuals
THREAT REPORT 2015 AT A GLANCE 2015 HIGHLIGHTS A few of the major events in 2015 concerning security issues. 08 07/15: Hacking Team 07/15: Bugs prompt 02/15: Europol joint breached, data Ford, Range Rover, 08/15: Google patches op takes down Ramnit released online Prius, Chrysler recalls Android Stagefright botnet flaw 09/15: XcodeGhost 07/15: Android 07/15: FBI Darkode tainted apps prompts Stagefright flaw 08/15: Amazon, ENFORCEMENT bazaar shutdown ATTACKS AppStore cleanup VULNERABILITY reported SECURITYPRODUCT Chrome drop Flash ads TOP MALWARE BREACHING THE MEET THE DUKES FAMILIES WALLED GARDEN The Dukes are a well- 12 18 resourced, highly 20 Njw0rm was the most In late 2015, the Apple App prominent new malware family in 2015. Store saw a string of incidents where dedicated and organized developers had used compromised tools cyberespionage group believed to be to unwittingly create apps with malicious working for the Russian Federation since behavior. The apps were able to bypass at least 2008 to collect intelligence in Njw0rm Apple’s review procedures to gain entry support of foreign and security policy decision-making. Angler into the store, and from there into an ordinary user’s iOS device. Gamarue THE CHAIN OF THE CHAIN OF Dorkbot COMPROMISE COMPROMISE: 23 The Stages 28 The Chain of Compromise Nuclear is a user-centric model that illustrates Kilim how cyber attacks combine different Ippedo techniques and resources to compromise Dridex devices and networks. It is defined by 4 main phases: Inception, Intrusion, WormLink Infection, and Invasion. INCEPTION Redirectors wreak havoc on US, Europe (p.28) INTRUSION AnglerEK dominates Flash (p.29) INFECTION The rise of rypto-ransomware (p.31) THREATS BY REGION Europe was particularly affected by the Angler exploit kit. -

Internet Security Threat Report VOLUME 21, APRIL 2016 TABLE of CONTENTS 2016 Internet Security Threat Report 2
Internet Security Threat Report VOLUME 21, APRIL 2016 TABLE OF CONTENTS 2016 Internet Security Threat Report 2 CONTENTS 4 Introduction 21 Tech Support Scams Go Nuclear, 39 Infographic: A New Zero-Day Vulnerability Spreading Ransomware Discovered Every Week in 2015 5 Executive Summary 22 Malvertising 39 Infographic: A New Zero-Day Vulnerability Discovered Every Week in 2015 8 BIG NUMBERS 23 Cybersecurity Challenges For Website Owners 40 Spear Phishing 10 MOBILE DEVICES & THE 23 Put Your Money Where Your Mouse Is 43 Active Attack Groups in 2015 INTERNET OF THINGS 23 Websites Are Still Vulnerable to Attacks 44 Infographic: Attackers Target Both Large and Small Businesses 10 Smartphones Leading to Malware and Data Breaches and Mobile Devices 23 Moving to Stronger Authentication 45 Profiting from High-Level Corporate Attacks and the Butterfly Effect 10 One Phone Per Person 24 Accelerating to Always-On Encryption 45 Cybersecurity, Cybersabotage, and Coping 11 Cross-Over Threats 24 Reinforced Reassurance with Black Swan Events 11 Android Attacks Become More Stealthy 25 Websites Need to Become Harder to 46 Cybersabotage and 12 How Malicious Video Messages Could Attack the Threat of “Hybrid Warfare” Lead to Stagefright and Stagefright 2.0 25 SSL/TLS and The 46 Small Business and the Dirty Linen Attack Industry’s Response 13 Android Users under Fire with Phishing 47 Industrial Control Systems and Ransomware 25 The Evolution of Encryption Vulnerable to Attacks 13 Apple iOS Users Now More at Risk than 25 Strength in Numbers 47 Obscurity is No Defense -
Digital Vision Network 5000 Series BCM Motherboard BIOS Upgrade
Digital Vision Network 5000 Series BCM™ Motherboard BIOS Upgrade Instructions October, 2011 24-10129-128 Rev. – Copyright 2011 Johnson Controls, Inc. All Rights Reserved (805) 522-5555 www.johnsoncontrols.com No part of this document may be reproduced without the prior permission of Johnson Controls, Inc. Cardkey P2000, BadgeMaster, and Metasys are trademarks of Johnson Controls, Inc. All other company and product names are trademarks or registered trademarks of their respective owners. These instructions are supplemental. Some times they are supplemental to other manufacturer’s documentation. Never discard other manufacturer’s documentation. Publications from Johnson Controls, Inc. are not intended to duplicate nor replace other manufacturer’s documentation. Due to continuous development of our products, the information in this document is subject to change without notice. Johnson Controls, Inc. shall not be liable for errors contained herein or for incidental or consequential damages in connection with furnishing or use of this material. Contents of this publication may be preliminary and/or may be changed at any time without any obligation to notify anyone of such revision or change, and shall not be regarded as a warranty. If this document is translated from the original English version by Johnson Controls, Inc., all reasonable endeavors will be used to ensure the accuracy of translation. Johnson Controls, Inc. shall not be liable for any translation errors contained herein or for incidental or consequential damages in connection -
Guide to Enterprise Patch Management Technologies
NIST Special Publication 800-40 Revision 3 Guide to Enterprise Patch Management Technologies Murugiah Souppaya Karen Scarfone C O M P U T E R S E C U R I T Y NIST Special Publication 800-40 Revision 3 Guide to Enterprise Patch Management Technologies Murugiah Souppaya Computer Security Division Information Technology Laboratory Karen Scarfone Scarfone Cybersecurity Clifton, VA July 2013 U.S. Department of Commerce Penny Pritzker, Secretary National Institute of Standards and Technology Patrick D. Gallagher, Under Secretary of Commerce for Standards and Technology and Director Authority This publication has been developed by NIST to further its statutory responsibilities under the Federal Information Security Management Act (FISMA), Public Law (P.L.) 107-347. NIST is responsible for developing information security standards and guidelines, including minimum requirements for Federal information systems, but such standards and guidelines shall not apply to national security systems without the express approval of appropriate Federal officials exercising policy authority over such systems. This guideline is consistent with the requirements of the Office of Management and Budget (OMB) Circular A-130, Section 8b(3), Securing Agency Information Systems, as analyzed in Circular A- 130, Appendix IV: Analysis of Key Sections. Supplemental information is provided in Circular A-130, Appendix III, Security of Federal Automated Information Resources. Nothing in this publication should be taken to contradict the standards and guidelines made mandatory and binding on Federal agencies by the Secretary of Commerce under statutory authority. Nor should these guidelines be interpreted as altering or superseding the existing authorities of the Secretary of Commerce, Director of the OMB, or any other Federal official. -
The Dark Reality of Open Source Spotlight Report
SPOTLIGHT The Dark Reality of Open Source Through the Lens of Threat and Vulnerability Management RiskSense Spotlight Report • May 2020 Executive Summary Open sourCe software (OSS) has quiCkly transformed both And while Heartbleed and the Apache Struts how modern applications are built and the underlying code vulnerabilities are the household names of open source they rely on. Access to high-quality and powerful open vulnerabilities, they are far from the only examples. Open source software projects has allowed developers to quickly source software is increasingly being targeted by integrate new capabilities into their applications without cryptominers, ransomware, and leveraged in DDoS having to reinvent the wheel. As a result, it is now estimated attacks. Unfortunately, OSS vulnerabilities are often a that between 80% and 90% of the code in most modern blind spot for many enterprises, who may not always be applications is made up of open source components. aware of all the open source projects and dependencies Likewise, many of the very tools that have enabled the that are used in their applications. growth of DevOps and CI/CD such as Jenkins, Kubernetes, and Docker are themselves open source projects. With this in mind, we have focused this version of the RiskSense Spotlight report on vulnerabilities in some of OSS also allows organizations to reduce their software today’s most popular open source software, including costs, and is often key to digital transformation efforts more than 50 OSS projects and over 2,600 vulnerabilities. and the transition of services to the cloud. It is no We then used this dataset to provide a risk-based surprise then that a 2020 report from Red Hat found that analysis of open source software to reveal the following: 95% of organizations view open source software as strategically important to their business. -

APT and Cybercriminal Targeting of HCS June 9, 2020 Agenda
APT and Cybercriminal Targeting of HCS June 9, 2020 Agenda • Executive Summary Slides Key: • APT Group Objectives Non-Technical: managerial, strategic • APT Groups Targeting Health Sector and high-level (general audience) • Activity Timeline Technical: Tactical / IOCs; requiring • TTPs in-depth knowledge (sysadmins, IRT) • Malware • Vulnerabilities • Recommendations and Mitigations TLP: WHITE, ID#202006091030 2 Executive Summary • APT groups steal data, disrupt operations, and destroy infrastructure. Unlike most cybercriminals, APT attackers pursue their objectives over longer periods of time. They adapt to cyber defenses and frequently retarget the same victim. • Common HPH targets include: • Healthcare Biotechnology Medical devices • Pharmaceuticals Healthcare information technology • Scientific research • HPH organizations who have been victim of APT attacks have suffered: • Reputational harm Disruption to operations • Financial losses PII/PHI and proprietary data theft • HC3 recommends several mitigations and controls to counter APT threats. TLP: WHITE, ID#202006091030 3 APT Group Objectives • Motivations of APT Groups which target the health sector include: • Competitive advantage • Theft of proprietary data/intellectual capital such as technology, manufacturing processes, partnership agreements, business plans, pricing documents, test results, scientific research, communications, and contact lists to unfairly advance economically. • Intelligence gathering • Groups target individuals and connected associates to further social engineering -

Backdoors in Software: a Cycle of Fear and Uncertainty
BACKDOORS IN SOFTWARE: A CYCLE OF FEAR AND UNCERTAINTY Leah Holden, Tufts University, Medford, MA Abstract: With the advent of cryptography and an increasingly online world, an antagonist to the security provided by encryption has emerged: backdoors. Backdoors are slated as insidious but often they aren’t intended to be. Backdoors can just be abused maintenance accounts, exploited vulnerabilities, or created by another agent via infecting host servers with malware. We cannot ignore that they may also be intentionally programmed into the source code of an application. Like with the cyber attrition problem, it may be difficult to determine the root cause of a backdoor and challenging to prove its very existence. These characteristics of backdoors ultimately lead to a state of being that I liken to a cycle of fear where governments or companies throw accusations around, the public roasts the accused, and other companies live in fear of being next. Notably missing from this cycle are any concrete solutions for preventing backdoors. A pervasive problem underlies this cycle: backdoors could be mitigated if software developers and their managers fully embraced the concept that no one should ever be able to bypass authentication. From the Clipper chip to the FBI and Apple’s standoff, we will examine requested, suspected, and proven backdoors up through the end of 2017. We will also look at the aftermath of these incidents and their effect on the relationship between software and government. Introduction: A backdoor has been defined as both “an undocumented portal that allows an administrator to enter the system to troubleshoot or do upkeep” and “ a secret portal that hackers and intelligence agencies used to gain illicit access” (Zetter). -

Android 10 OS Update Instruction for Family of Products on SDM660
Android 10 OS Update Instruction for Family of Products on SDM660 1 Contents 1. A/B (Seamless) OS Update implementation on SDM660 devices ................................................................................................... 2 2. How AB system is different to Non-AB system ............................................................................................................................... 3 3. Android AB Mode for OS Update .................................................................................................................................................... 4 4. Recovery Mode for OS Update ........................................................................................................................................................ 4 5. Reset Packages and special recovery packages ................................................................................................................................ 4 6. OS Upgrade and Downgrade ............................................................................................................................................................ 5 7. OS Upgrade and Downgrade via EMMs .......................................................................................................................................... 6 8. AB Streaming Update ....................................................................................................................................................................... 7 9. User Notification for Full OTA package -

A PRACTICAL METHOD of IDENTIFYING CYBERATTACKS February 2018 INDEX
In Collaboration With A PRACTICAL METHOD OF IDENTIFYING CYBERATTACKS February 2018 INDEX TOPICS EXECUTIVE SUMMARY 4 OVERVIEW 5 THE RESPONSES TO A GROWING THREAT 7 DIFFERENT TYPES OF PERPETRATORS 10 THE SCOURGE OF CYBERCRIME 11 THE EVOLUTION OF CYBERWARFARE 12 CYBERACTIVISM: ACTIVE AS EVER 13 THE ATTRIBUTION PROBLEM 14 TRACKING THE ORIGINS OF CYBERATTACKS 17 CONCLUSION 20 APPENDIX: TIMELINE OF CYBERSECURITY 21 INCIDENTS 2 A Practical Method of Identifying Cyberattacks EXECUTIVE OVERVIEW SUMMARY The frequency and scope of cyberattacks Cyberattacks carried out by a range of entities are continue to grow, and yet despite the seriousness a growing threat to the security of governments of the problem, it remains extremely difficult to and their citizens. There are three main sources differentiate between the various sources of an of attacks; activists, criminals and governments, attack. This paper aims to shed light on the main and - based on the evidence - it is sometimes types of cyberattacks and provides examples hard to differentiate them. Indeed, they may of each. In particular, a high level framework sometimes work together when their interests for investigation is presented, aimed at helping are aligned. The increasing frequency and severity analysts in gaining a better understanding of the of the attacks makes it more important than ever origins of threats, the motive of the attacker, the to understand the source. Knowing who planned technical origin of the attack, the information an attack might make it easier to capture the contained in the coding of the malware and culprits or frame an appropriate response. the attacker’s modus operandi. -
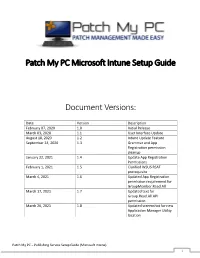
Patch My PC Microsoft Intune Setup Guide Document Versions
Patch My PC Microsoft Intune Setup Guide Document Versions: Date Version Description February 07, 2020 1.0 Initial Release March 03, 2020 1.1 User Interface Update August 18, 2020 1.2 Intune Update Feature September 24, 2020 1.3 Grammar and App Registration permission cleanup January 22, 2021 1.4 Update App Registration Permissions February 1, 2021 1.5 Clarified WSUS RSAT prerequisite March 4, 2021 1.6 Updated App Registration permission requirement for GroupMember.Read.All March 17, 2021 1.7 Updated text for Group.Read.All API permission March 26, 2021 1.8 Updated screenshot for new Application Manager Utility location Patch My PC – Publishing Service Setup Guide (Microsoft Intune) 1 System Requirements: • Microsoft .NET Framework 4.5 • Supported Operating Systems o Windows Server 2008 o Windows Server 2012 o Windows Server 2016 o Windows Server 2019 o Windows 10 (x64) – Microsoft Intune only Prerequisites: • WSUS Remote Server Administration Tools (RSAT) to be installed Download the latest MSI installer of the publishing service using the following URL: https://patchmypc.com/publishing- service-download Start the installation by double- clicking the downloaded MSI. Note: Depending on user account control settings, you may need to run an elevated command prompt and launch the MSI from the command prompt. Click Next in the Welcome Wizard Click Next in the Installation Folder Dialog Optionally, you can change the installation folder by clicking Browse… Click Install on the Ready to Install dialog. Note: if user-account control is enabled, you will receive a prompt “Do you want to allow this app to make changes to your device?” Click Yes on this prompt to allow installation Patch My PC – Publishing Service Setup Guide (Microsoft Intune) 2 If you are configuring the product for Intune Win32 application publishing only, you can check Enable Microsoft Intune standalone mode When this option is enabled, prerequisite checks related to WSUS and Configuration Manager are skipped.