Apple Filing Protocol Afp
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-

Open Source Solutions for Building Your Own Storage Area Network and Network Attached Storage
Open Source Solutions for Building Your Own Storage Area Network and Network Attached Storage Author, Balakrishnan Subramanian A Data Science Foundation White Paper May 2020 --------------------------------------------------- Data Science Foundation Data Science Foundation, Atlantic Business Centre, Atlantic Street, Altrincham, WA14 5NQ Tel: 0161 926 3641 Email: [email protected] Web: www.datascience.foundation Registered in England and Wales 4th June 2015, Registered Number 9624670 www.datascience.foundation Copyright 2016 - 2017 Data Science Foundation 1. INTRODUCTION Generally, Storage solutions can be grouped into following four categories: SoHo NAS systems, Cloud-based/object solutions, Microsoft Storage Server solutions, Enterprise NAS (Networked Attached Storage) and Storage Area Network (SAN) solutions. Enterprise NAS and SAN solutions are generally closed systems offered by traditional vendors like EMC and NetApp with a very large price tag, so many businesses are looking at Open Source solutions to meet their needs. This is a collection of links and brief descriptions of Open Source storage solutions currently available. Open Source of course means it’s free to use and modify, however some projects have do commercially supported versions as well for enterprise customers who require it. 1. Factors for choosing Storage Solutions When you are in the need of Storage solutions for managing your own infrastructure in your private Data Center, there are many offerings but selecting the right one depends upon your requirement. Factors involved in selecting a Storage type Budget Type of Data that you want to store Scaling concerns and Usage pattern In this article, we will be discussing two different methods (i.e. NAS and SAN), these two methods define the Structure of the storage, it is important to choose the right one based upon your use case and type of data. -
IPS Signature Release Note V9.17.79
SOPHOS IPS Signature Update Release Notes Version : 9.17.79 Release Date : 19th January 2020 IPS Signature Update Release Information Upgrade Applicable on IPS Signature Release Version 9.17.78 CR250i, CR300i, CR500i-4P, CR500i-6P, CR500i-8P, CR500ia, CR500ia-RP, CR500ia1F, CR500ia10F, CR750ia, CR750ia1F, CR750ia10F, CR1000i-11P, CR1000i-12P, CR1000ia, CR1000ia10F, CR1500i-11P, CR1500i-12P, CR1500ia, CR1500ia10F Sophos Appliance Models CR25iNG, CR25iNG-6P, CR35iNG, CR50iNG, CR100iNG, CR200iNG/XP, CR300iNG/XP, CR500iNG- XP, CR750iNG-XP, CR2500iNG, CR25wiNG, CR25wiNG-6P, CR35wiNG, CRiV1C, CRiV2C, CRiV4C, CRiV8C, CRiV12C, XG85 to XG450, SG105 to SG650 Upgrade Information Upgrade type: Automatic Compatibility Annotations: None Introduction The Release Note document for IPS Signature Database Version 9.17.79 includes support for the new signatures. The following sections describe the release in detail. New IPS Signatures The Sophos Intrusion Prevention System shields the network from known attacks by matching the network traffic against the signatures in the IPS Signature Database. These signatures are developed to significantly increase detection performance and reduce the false alarms. Report false positives at [email protected], along with the application details. January 2020 Page 2 of 245 IPS Signature Update This IPS Release includes Two Thousand, Seven Hundred and Sixty Two(2762) signatures to address One Thousand, Nine Hundred and Thirty Eight(1938) vulnerabilities. New signatures are added for the following vulnerabilities: Name CVE–ID -

Mac OS X Server Administrator's Guide
034-9285.S4AdminPDF 6/27/02 2:07 PM Page 1 Mac OS X Server Administrator’s Guide K Apple Computer, Inc. © 2002 Apple Computer, Inc. All rights reserved. Under the copyright laws, this publication may not be copied, in whole or in part, without the written consent of Apple. The Apple logo is a trademark of Apple Computer, Inc., registered in the U.S. and other countries. Use of the “keyboard” Apple logo (Option-Shift-K) for commercial purposes without the prior written consent of Apple may constitute trademark infringement and unfair competition in violation of federal and state laws. Apple, the Apple logo, AppleScript, AppleShare, AppleTalk, ColorSync, FireWire, Keychain, Mac, Macintosh, Power Macintosh, QuickTime, Sherlock, and WebObjects are trademarks of Apple Computer, Inc., registered in the U.S. and other countries. AirPort, Extensions Manager, Finder, iMac, and Power Mac are trademarks of Apple Computer, Inc. Adobe and PostScript are trademarks of Adobe Systems Incorporated. Java and all Java-based trademarks and logos are trademarks or registered trademarks of Sun Microsystems, Inc. in the U.S. and other countries. Netscape Navigator is a trademark of Netscape Communications Corporation. RealAudio is a trademark of Progressive Networks, Inc. © 1995–2001 The Apache Group. All rights reserved. UNIX is a registered trademark in the United States and other countries, licensed exclusively through X/Open Company, Ltd. 062-9285/7-26-02 LL9285.Book Page 3 Tuesday, June 25, 2002 3:59 PM Contents Preface How to Use This Guide 39 What’s Included -

Cygwin User's Guide
Cygwin User’s Guide Cygwin User’s Guide ii Copyright © Cygwin authors Permission is granted to make and distribute verbatim copies of this documentation provided the copyright notice and this per- mission notice are preserved on all copies. Permission is granted to copy and distribute modified versions of this documentation under the conditions for verbatim copying, provided that the entire resulting derived work is distributed under the terms of a permission notice identical to this one. Permission is granted to copy and distribute translations of this documentation into another language, under the above conditions for modified versions, except that this permission notice may be stated in a translation approved by the Free Software Foundation. Cygwin User’s Guide iii Contents 1 Cygwin Overview 1 1.1 What is it? . .1 1.2 Quick Start Guide for those more experienced with Windows . .1 1.3 Quick Start Guide for those more experienced with UNIX . .1 1.4 Are the Cygwin tools free software? . .2 1.5 A brief history of the Cygwin project . .2 1.6 Highlights of Cygwin Functionality . .3 1.6.1 Introduction . .3 1.6.2 Permissions and Security . .3 1.6.3 File Access . .3 1.6.4 Text Mode vs. Binary Mode . .4 1.6.5 ANSI C Library . .4 1.6.6 Process Creation . .5 1.6.6.1 Problems with process creation . .5 1.6.7 Signals . .6 1.6.8 Sockets . .6 1.6.9 Select . .7 1.7 What’s new and what changed in Cygwin . .7 1.7.1 What’s new and what changed in 3.2 . -

Softnas Deployment Guide for High- Performance SQL Storage
SoftNAS Deployment Guide for High- Performance SQL Storage Introduction SoftNAS cloud NAS systems are based on an innovative, memory-centric storage architecture that delivers unparalleled NAS performance, efficiency, and value. They incorporate a hybrid disk storage technology that tailors the usage of data disks, log solid- state cache drives (SSDs), and read cache SSDs to the data share's specific needs. Additional features include variable storage record size, data compression, and multiple connectivity options. As a Cloud NAS solution, SoftNAS cloud NAS systems provide an excellent base for Microsoft Windows Server deployments by providing iSCSI or Fibre Channel block storage for Microsoft SQL Server, and network file system (NFS) or server message block (SMB) file storage for Microsoft Windows client access. This document covers the best practices to follow when deploying Microsoft SQL Server on a SoftNAS cloud NAS system. The intended audience is storage administrators and Microsoft SQL Server database administrators. Maintaining High Availability As with any business-critical application, high availability is a crucial design criterion to be considered when deploying a Microsoft SQL Server installation. Microsoft SQL Server 2016 can be installed on local and/or shared file systems, and SoftNAS cloud NAS systems can satisfy both of these options. Local file systems (from the Microsoft Windows Server perspective) are hosted as block volumes—iSCSI and/or Fibre-Channel-connected LUNs and file systems as SMB and/or NFS volumes. High availability starts with the network connectivity supporting the storage and server interconnectivity. Any design for the storage infrastructure should avoid single points of failure. Because many white papers and publications cover storage-area networking and network-attached storage resilience, those topics are not covered in detail in this paper. -

11.7 the Windows 2000 File System
830 CASE STUDY 2: WINDOWS 2000 CHAP. 11 11.7 THE WINDOWS 2000 FILE SYSTEM Windows 2000 supports several file systems, the most important of which are FAT-16, FAT-32, and NTFS (NT File System). FAT-16 is the old MS-DOS file system. It uses 16-bit disk addresses, which limits it to disk partitions no larger than 2 GB. FAT-32 uses 32-bit disk addresses and supports disk partitions up to 2 TB. NTFS is a new file system developed specifically for Windows NT and car- ried over to Windows 2000. It uses 64-bit disk addresses and can (theoretically) support disk partitions up to 264 bytes, although other considerations limit it to smaller sizes. Windows 2000 also supports read-only file systems for CD-ROMs and DVDs. It is possible (even common) to have the same running system have access to multiple file system types available at the same time. In this chapter we will treat the NTFS file system because it is a modern file system unencumbered by the need to be fully compatible with the MS-DOS file system, which was based on the CP/M file system designed for 8-inch floppy disks more than 20 years ago. Times have changed and 8-inch floppy disks are not quite state of the art any more. Neither are their file systems. Also, NTFS differs both in user interface and implementation in a number of ways from the UNIX file system, which makes it a good second example to study. NTFS is a large and complex system and space limitations prevent us from covering all of its features, but the material presented below should give a reasonable impression of it. -
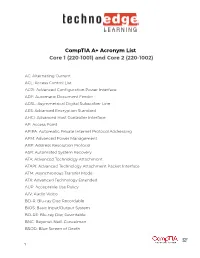
Comptia A+ Acronym List Core 1 (220-1001) and Core 2 (220-1002)
CompTIA A+ Acronym List Core 1 (220-1001) and Core 2 (220-1002) AC: Alternating Current ACL: Access Control List ACPI: Advanced Configuration Power Interface ADF: Automatic Document Feeder ADSL: Asymmetrical Digital Subscriber Line AES: Advanced Encryption Standard AHCI: Advanced Host Controller Interface AP: Access Point APIPA: Automatic Private Internet Protocol Addressing APM: Advanced Power Management ARP: Address Resolution Protocol ASR: Automated System Recovery ATA: Advanced Technology Attachment ATAPI: Advanced Technology Attachment Packet Interface ATM: Asynchronous Transfer Mode ATX: Advanced Technology Extended AUP: Acceptable Use Policy A/V: Audio Video BD-R: Blu-ray Disc Recordable BIOS: Basic Input/Output System BD-RE: Blu-ray Disc Rewritable BNC: Bayonet-Neill-Concelman BSOD: Blue Screen of Death 1 BYOD: Bring Your Own Device CAD: Computer-Aided Design CAPTCHA: Completely Automated Public Turing test to tell Computers and Humans Apart CD: Compact Disc CD-ROM: Compact Disc-Read-Only Memory CD-RW: Compact Disc-Rewritable CDFS: Compact Disc File System CERT: Computer Emergency Response Team CFS: Central File System, Common File System, or Command File System CGA: Computer Graphics and Applications CIDR: Classless Inter-Domain Routing CIFS: Common Internet File System CMOS: Complementary Metal-Oxide Semiconductor CNR: Communications and Networking Riser COMx: Communication port (x = port number) CPU: Central Processing Unit CRT: Cathode-Ray Tube DaaS: Data as a Service DAC: Discretionary Access Control DB-25: Serial Communications -

Github: a Case Study of Linux/BSD Perceptions from Microsoft's
1 FLOSS != GitHub: A Case Study of Linux/BSD Perceptions from Microsoft’s Acquisition of GitHub Raula Gaikovina Kula∗, Hideki Hata∗, Kenichi Matsumoto∗ ∗Nara Institute of Science and Technology, Japan {raula-k, hata, matumoto}@is.naist.jp Abstract—In 2018, the software industry giants Microsoft made has had its share of disagreements with Microsoft [6], [7], a move into the Open Source world by completing the acquisition [8], [9], the only reported negative opinion of free software of mega Open Source platform, GitHub. This acquisition was not community has different attitudes towards GitHub is the idea without controversy, as it is well-known that the free software communities includes not only the ability to use software freely, of ‘forking’ so far, as it it is considered as a danger to FLOSS but also the libre nature in Open Source Software. In this study, development [10]. our aim is to explore these perceptions in FLOSS developers. We In this paper, we report on how external events such as conducted a survey that covered traditional FLOSS source Linux, acquisition of the open source platform by a closed source and BSD communities and received 246 developer responses. organization triggers a FLOSS developers such the Linux/ The results of the survey confirm that the free community did trigger some communities to move away from GitHub and raised BSD Free Software communities. discussions into free and open software on the GitHub platform. The study reminds us that although GitHub is influential and II. TARGET SUBJECTS AND SURVEY DESIGN trendy, it does not representative all FLOSS communities. -

OS X Support Essentials 10.9 Apple Pro Training Series
Apple Pro Training Series: OS X Support Essentials 10.9 Apple Pro Training Series Training Apple Pro Network Configuration Locations: One selected by user Automatic Work Home Test Ethernet Wi-Fi Ethernet 2 FireWire VPN Services: Multiple services activate and prioritized based on service order Understand OS X Mavericks underlying technologies, Configurestand-alone and networked Mac Troubleshoot software and hardware issues software components, and industry-standard protocols. computers with step-by-step instructions. using Apple-recommended procedures and tools. OS X Mavericks Supporting and Troubleshooting OS X Support Essentials 10.9 The Apple-Certified Way to Learn This is the official curriculum of the Apple Mavericks 101: OS X The Apple Pro Training Series is both a self-paced Support Essentials 10.9 course and preparation for Apple learning tool and the official curriculum of the Apple Training and Certified Support Professional (ACSP) 10.9 certification— Certification program. Upon completing the course material in this as well as a top-notch primer for anyone who needs to support, book, you can become an Apple Certified Support Professional by troubleshoot, or optimize OS X Mavericks. This guide provides passing the OS X Support Essentials 10.9 Exam. Work through this comprehensive coverage of Mavericks and is part of the Apple book as self-study material or attend a class at an Apple Authorized Pro Training series—the only Apple-certified books on the Training Center. To learn more, please visit training.apple.com. market. Designed for support technicians, help desk specialists, and ardent Mac users, this guide takes you deep inside the Also in the Apple Pro Training Series: Mavericks operating system. -

Nas Software
Nas software click here to download “I heard about FreeNAS at a conference and realized it was an immediate necessity for one of my clients. They had an existing NAS system that was not being. The Opensource Linux NAS software is light Linux Distros but enough power to handle your storage problem. You can build your own NAS. XigmaNAS is the easiest and quickest way to install an Open Source free NAS server. From home NAS to enterprise network storage, XigmaNAS is trusted by. Build and manage your own Linux & BTRFS powered advanced NAS and Cloud Storage is an essential part of many creative software and hardware projects. The following are four of the best NAS solutions for Linux that do the job software, so you can control and name all NAS-connected drives on. Here is a list of some best free and open source NAS Operating system available on the Internet and the way to backup Blu-ray/DVD/Video to. Related Article ➤ 9 Free Self Hosted Cloud Storage Software For Home network-attached storage (NAS) OS software for small businesses. Network-attached storage (NAS) is a file-level computer data storage server connected to a computer network providing data access to a heterogeneous group of clients. NAS is specialized for serving files either by its hardware, software. Inspired by the television show, Top Gear, I'd really like to maintain my own “Big Board” of NAS software where I rank them against each other. I recently bought a Dell T30, that i want to use as a NAS, Plex server, private cloud and file server. -

Computer Service Technician- CST Competency Requirements
Computer Service Technician- CST Competency Requirements This Competency listing serves to identify the major knowledge, skills, and training areas which the Computer Service Technician needs in order to perform the job of servicing the hardware and the systems software for personal computers (PCs). The present CST COMPETENCIES only address operating systems for Windows current version, plus three older. Included also are general common Linux and Apple competency information, as proprietary service contracts still keep most details specific to in-house service. The Competency is written so that it can be used as a course syllabus, or the study directed towards the education of individuals, who are expected to have basic computer hardware electronics knowledge and skills. Computer Service Technicians must be knowledgeable in the following technical areas: 1.0 SAFETY PROCEDURES / HANDLING / ENVIRONMENTAL AWARENESS 1.1 Explain the need for physical safety: 1.1.1 Lifting hardware 1.1.2 Electrical shock hazard 1.1.3 Fire hazard 1.1.4 Chemical hazard 1.2 Explain the purpose for Material Safety Data Sheets (MSDS) 1.3 Summarize work area safety and efficiency 1.4 Define first aid procedures 1.5 Describe potential hazards in both in-shop and in-home environments 1.6 Describe proper recycling and disposal procedures 2.0 COMPUTER ASSEMBLY AND DISASSEMBLY 2.1 List the tools required for removal and installation of all computer system components 2.2 Describe the proper removal and installation of a CPU 2.2.1 Describe proper use of Electrostatic Discharge -

File Systems
File Systems Profs. Bracy and Van Renesse based on slides by Prof. Sirer Storing Information • Applications could store information in the process address space • Why is this a bad idea? – Size is limited to size of virtual address space – The data is lost when the application terminates • Even when computer doesn’t crash! – Multiple process might want to access the same data File Systems • 3 criteria for long-term information storage: 1. Able to store very large amount of information 2. Information must survive the processes using it 3. Provide concurrent access to multiple processes • Solution: – Store information on disks in units called files – Files are persistent, only owner can delete it – Files are managed by the OS File Systems: How the OS manages files! File Naming • Motivation: Files abstract information stored on disk – You do not need to remember block, sector, … – We have human readable names • How does it work? – Process creates a file, and gives it a name • Other processes can access the file by that name – Naming conventions are OS dependent • Usually names as long as 255 characters is allowed • Windows names not case sensitive, UNIX family is File Extensions • Name divided into 2 parts: Name+Extension • On UNIX, extensions are not enforced by OS – Some applications might insist upon them • Think: .c, .h, .o, .s, etc. for C compiler • Windows attaches meaning to extensions – Tries to associate applications to file extensions File Access • Sequential access – read all bytes/records from the beginning – particularly convenient for magnetic tape • Random access – bytes/records read in any order – essential for database systems File Attributes • File-specific info maintained by the OS – File size, modification date, creation time, etc.