CPM 2.2 Alteration Guide
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-

GBCC-CIS-1 Page 1 Micro-Soft’S Macro-Impact
CIS111 GBCC Renee Dodge CIS111 Mid-Term – Fall 2010 For your mid-term, I would like you to conduct some research on the history of computers. Select a milestone or event that you feel had a significant impact on the overall development of computers and how we use computers today. Be sure you not only provide your opinion as to why you feel this milestone is significant, but also provide historical proof - actual facts as to how this event shaped the development and use of computers. For this assignment, please complete the following: 1. Choose a topic 2. Research your topic and locate at least 5 different sources of information, overall. o At least 3 sources should be Internet websites. o Remember: Wikipedia is NOT an acceptable research source. 3. In addition to the Internet, you should also utilize the library online resources (EBSCO database, e-Books, etc). o At least 2 different sources of information should be online library resources. o If you have never used the library online resources before, you may ask me for a brief overview of how to use them or see Becky Clerkin in the library for help. 4. Include your research findings in a 5-page paper and be sure to properly cite where you found your information. If you are not sure how to cite references check out the following link: How to Cite Books, Magazines, and Web Sites in a Research Paper: http://www.lib.duke.edu/libguide/works_cited.htm 5. Upload your research paper to the Digital Drop BoX no later than Wednesday, October 27th at 11:59pm. -

Adaptive Android Kernel Live Patching
Adaptive Android Kernel Live Patching Yue Chen Yulong Zhang Zhi Wang Liangzhao Xia Florida State University Baidu X-Lab Florida State University Baidu X-Lab Chenfu Bao Tao Wei Baidu X-Lab Baidu X-Lab Abstract apps contain sensitive personal data, such as bank ac- counts, mobile payments, private messages, and social Android kernel vulnerabilities pose a serious threat to network data. Even TrustZone, widely used as the se- user security and privacy. They allow attackers to take cure keystore and digital rights management in Android, full control over victim devices, install malicious and un- is under serious threat since the compromised kernel en- wanted apps, and maintain persistent control. Unfortu- ables the attacker to inject malicious payloads into Trust- nately, most Android devices are never timely updated Zone [42, 43]. Therefore, Android kernel vulnerabilities to protect their users from kernel exploits. Recent An- pose a serious threat to user privacy and security. droid malware even has built-in kernel exploits to take Tremendous efforts have been put into finding (and ex- advantage of this large window of vulnerability. An ef- ploiting) Android kernel vulnerabilities by both white- fective solution to this problem must be adaptable to lots hat and black-hat researchers, as evidenced by the sig- of (out-of-date) devices, quickly deployable, and secure nificant increase of kernel vulnerabilities disclosed in from misuse. However, the fragmented Android ecosys- Android Security Bulletin [3] in recent years. In ad- tem makes this a complex and challenging task. dition, many kernel vulnerabilities/exploits are publicly To address that, we systematically studied 1;139 An- available but never reported to Google or the vendors, droid kernels and all the recent critical Android ker- let alone patched (e.g., exploits in Android rooting nel vulnerabilities. -

A Guide to Discuss Ethical Issues in Digital Research Second Edition
Ethical challenges in digital research 2nd edition ETHICAL CHALLENGES IN DIGITAL RESEARCH A guide to discuss ethical issues in digital research Second edition Ethical challenges in digital research 2nd edition Ethical challenges in digital research – A guide to discuss ethical issues in digital research Second edition January 2020 Developed by DIGETIK at Aalborg University as part of DIGHUMLAB Authors Line Lisberg Christensen, Research Assistant Malene Charlotte Larsen, Associate Professor Layout Steffen Madsen, DIGHUMLAB i Ethical challenges in digital research 2nd edition I. Introduction to document The ever-changing development of digital technologies and digital infrastructure makes it necessary for us as researchers to change approaches to digital research within the humanities. In terms of research ethics, we can no longer use traditional laws and guidelines that only match the non-digital world. In a time where it is necessary to change and re-think our ways of doing research, we bring to you this second version of Ethical Challenges in Digital Research to initiate discussions about ethical research and to help guide you in your digital research. The compound may serve you as a guideline to ethical research, a helpful tool to those in need of inspiration or merely as a list of literature that is relevant to your field, whether that is: big data, surveillance, privacy, games and gamification, ethics in studies with children and adolescents, health research, journalism, ethnographic studies, visual methods, vulnerable groups, web archives, economy, risky business for researchers or one of the many other categories in this collection of ethical digital research. We initially created this document with the intention of helping scholars reflect and discuss the ethical dimensions of their digital research, whilst providing guidance and insight about how to deal with these issues. -

Concurrent CP/M-86 User's Guide 1.1 What Concurrent CP/M-86 Is
Concurrent CP/M-86™ Operating System Concurrent CP/M-86™ Operating System User's Guide Copyright © 1982 Digital Research P.O. Box -579 160 Central Avenue Pacific Grove, CA 93950 (408) 649-3896 TWX 910 360 5001 All Rights Reserved COPYRIGHT Copyr ight © 1982 by Digi tal Research. All r igh ts reserved. No part of this pUblication may be reproduced, transmitted, transcribed, stored in a retrieval system, or translated into any language or compu ter language, in any form or by any means, electronic, mechanical, magnetic, optical, chemical, manual or otherwise, without the prior written permiss ion of Digital Research, Post Off ice Box 579, Pacific Grove, California, 93950. This manual is, however, tutorial in nature. Thus, the reader is granted permission to include the example programs, either in whole or in part, in his own programs. DISCLAIMER Digital Research makes no representations or warranties with respect to the contents hereof and specifically disclaims any ,implied warranties of merchantabil i ty or fitness for any particular purpose. Further, Digital Research reserves the right to revise this publication and to make changes f rom time to time in the content hereof wi thou t obligation of Digital Research to notify any person of such revision or changes. TRADEMARKS CP/M is a registered trademark of Digital Research. ASM-86, CP/M-86, Concurrent CP/M-86 and DDT-86 are trademarks of Digital Research. ED and TEX are utilities of Digital Research. Intel is a registered trademark of Intel Corporation. The IBM Personal Computer is a trade name of International Business Machines. -
Digital Vision Network 5000 Series BCM Motherboard BIOS Upgrade
Digital Vision Network 5000 Series BCM™ Motherboard BIOS Upgrade Instructions October, 2011 24-10129-128 Rev. – Copyright 2011 Johnson Controls, Inc. All Rights Reserved (805) 522-5555 www.johnsoncontrols.com No part of this document may be reproduced without the prior permission of Johnson Controls, Inc. Cardkey P2000, BadgeMaster, and Metasys are trademarks of Johnson Controls, Inc. All other company and product names are trademarks or registered trademarks of their respective owners. These instructions are supplemental. Some times they are supplemental to other manufacturer’s documentation. Never discard other manufacturer’s documentation. Publications from Johnson Controls, Inc. are not intended to duplicate nor replace other manufacturer’s documentation. Due to continuous development of our products, the information in this document is subject to change without notice. Johnson Controls, Inc. shall not be liable for errors contained herein or for incidental or consequential damages in connection with furnishing or use of this material. Contents of this publication may be preliminary and/or may be changed at any time without any obligation to notify anyone of such revision or change, and shall not be regarded as a warranty. If this document is translated from the original English version by Johnson Controls, Inc., all reasonable endeavors will be used to ensure the accuracy of translation. Johnson Controls, Inc. shall not be liable for any translation errors contained herein or for incidental or consequential damages in connection -
Guide to Enterprise Patch Management Technologies
NIST Special Publication 800-40 Revision 3 Guide to Enterprise Patch Management Technologies Murugiah Souppaya Karen Scarfone C O M P U T E R S E C U R I T Y NIST Special Publication 800-40 Revision 3 Guide to Enterprise Patch Management Technologies Murugiah Souppaya Computer Security Division Information Technology Laboratory Karen Scarfone Scarfone Cybersecurity Clifton, VA July 2013 U.S. Department of Commerce Penny Pritzker, Secretary National Institute of Standards and Technology Patrick D. Gallagher, Under Secretary of Commerce for Standards and Technology and Director Authority This publication has been developed by NIST to further its statutory responsibilities under the Federal Information Security Management Act (FISMA), Public Law (P.L.) 107-347. NIST is responsible for developing information security standards and guidelines, including minimum requirements for Federal information systems, but such standards and guidelines shall not apply to national security systems without the express approval of appropriate Federal officials exercising policy authority over such systems. This guideline is consistent with the requirements of the Office of Management and Budget (OMB) Circular A-130, Section 8b(3), Securing Agency Information Systems, as analyzed in Circular A- 130, Appendix IV: Analysis of Key Sections. Supplemental information is provided in Circular A-130, Appendix III, Security of Federal Automated Information Resources. Nothing in this publication should be taken to contradict the standards and guidelines made mandatory and binding on Federal agencies by the Secretary of Commerce under statutory authority. Nor should these guidelines be interpreted as altering or superseding the existing authorities of the Secretary of Commerce, Director of the OMB, or any other Federal official. -
OS 386 Multiuser/Multitasking Operating System
OS 386 Multiuser/Multitasking Operating System REFERENCE GUIDE [Q] DIGITAL RESEARCH@ os REFERENCE GUIDE [jill DIGITAL RESEARCH~ COPYRIGHT Copyright © 1987 Digital Research Inc. All rights reserved. No part of this publication may be reproduced, transcribed, stored in a retrieval system, or translated into any language or computer language, in any form or by any means, electronic, mechanical, magnetic, optical, chemical, manual or otherwise without the prior written permission of Digital Research Inc, 60 Garden Court, Box DRI, Monterey, California 93942 DISCLAIMER DIGITAL RESEARCH MAKES NO REPRESENTATIONS OR WARRANTIES WITH RESPECT TO THE CONTENTS HEREOF AND SPECIFICALLY DISCLAIMS ANY IMPLIED WARRANTIES OF MERCHANTABILITY OR FITNESS FOR ANY PARTICULAR PURPOSE. Further Digital Research Inc. reserves the right to revise this publication and to make changes from time to time in the content hereof without obligation of Digital Research Inc to notify any person of such revision or changes. NOTICE TO USER This manual should not be construed as any representation or warranty with respect to the software named herein. Occasionally changes or variations exist in the software that are not reflected in the manual. Generally, if such changes or variations are known to exist and to affect the product significantly, a release note or READ.ME file accompanies the manual and the distribution disks. In that event, be sure to read the release note or READ.ME file before using the product. ii TRADEMARKS Digital Research and its logo, CP/M, and CP/M-86 are registered trademarks of Digital Research Inc. Cardfile, Concurrent, Concurrent DOS 386, Concurrent DOS XM, DR EDIX, DOS Plus and MP/M-86 are trademarks of Digital Research Inc. -

MSP430 Family Object Format Converter Description 10-1 Topics
MSP430 Family Object Format Converter Description Topics 10 Object Format Converter Description 10-3 10.1 Object Format Converter Development Flow 10-4 10.2 Extended Tektronix Hex Object Format 10-5 10.3 Intel Hex Object Format 10-6 10.4 TI–Tagged Object Format 10-7 10.5 Motorola S Format 10-8 10.6 Invoking the Object Format Converter 10-9 10.7 Object Format Converter Examples 10-10 10.8 Halt Conditions 10-11 Figures Fig. Title Page 10.1 Object Format Converter Development Flow 10-4 10.2 Extended Tektronix Hex Object Format 10-5 10.3 Intel Hex Object Format 10-6 10.4 TI–Tagged Object Format 10-7 10.5 Motorola S Format 10-8 10-1 Object Format Converter Description MSP430 Family 10-2 MSP430 Family Object Format Converter Description 10 Object Format Converter Description Most EPROM programmers do not accept COFF object files as input. The object format converter converts a COFF object file into one of four object formats that most EPROM programmers accept as input: Extended Tektronix hex object format supports 32–bit addresses. Intel hex object format supports 16–bit addresses. Motorola S format supports 16–bit addresses. TI–tagged object format supports 16–bit addresses. 10-3 Object Format Converter Description MSP430 Family 10.1 Object Format Converter Development Flow The figure illustrates the object format converter's role in the assembly language development process. Macro Assembler Source Files Source Archiver Assembler Macro Library COFF Object Files Linker Archiver Library of Executable Object Files COFF Objekt Files Object Format Converter EPROM Absolute Software Evaluation In-Circuit MSP430 Programmer Lister Emulator Module Emulator Figure 10.1: Object Format Converter Development Flow 10-4 MSP430 Family Object Format Converter Description 10.2 Extended Tektronix Hex Object Format The Extended Tektronix hex object format supports 32–bit addresses and has three types of records: data, symbol, and termination records. -

Android 10 OS Update Instruction for Family of Products on SDM660
Android 10 OS Update Instruction for Family of Products on SDM660 1 Contents 1. A/B (Seamless) OS Update implementation on SDM660 devices ................................................................................................... 2 2. How AB system is different to Non-AB system ............................................................................................................................... 3 3. Android AB Mode for OS Update .................................................................................................................................................... 4 4. Recovery Mode for OS Update ........................................................................................................................................................ 4 5. Reset Packages and special recovery packages ................................................................................................................................ 4 6. OS Upgrade and Downgrade ............................................................................................................................................................ 5 7. OS Upgrade and Downgrade via EMMs .......................................................................................................................................... 6 8. AB Streaming Update ....................................................................................................................................................................... 7 9. User Notification for Full OTA package -

Sqtp File Format Specification
SQTP FILE FORMAT SPECIFICATION SQTPSM File Format Specification INTRODUCTION This document shows how a Serial Quick Turn Programming (SQTPSM) file is produced and used by MPLAB® IPE Integrated Programming Environment. Engineers can use this information to generate their own SQTP file. • Overview • Example SQTP File • Intel HEX File Format • MPLAB IPE SQTP File Generation • Customer Generated SQTP Files • Programming of Devices • Understanding Usage of RETLW in SQTP File for Midrange and Baseline Devices • Examples of SQTP Files for Various Memory Regions • Differences in SQTP File Behavior Between MPLAB IPE v2.35 (and Before) and MPLAB IPE v2.40 (and Later) • Differences in the SQTP Feature Between MPLAB IDE v8.xx and MPLAB IPE for the Flash Data Memory Region OVERVIEW Serialization is a method of programming microcontrollers whereby each chip is pro- grammed with a slightly different code. Typically, all locations are programmed with the same basic code, except for a few contiguous bytes. Those bytes are programmed with a different number (referred to as “key” or “ID number” or “serial number”) in a program region. Typical applications for such programming are where each unit must have a different access code, as in the Internet of Things (IoT), car alarms or garage door openers. An SQTP file (.num) contains the serial numbers to be used as each device is programmed. Microchip devices require that the serial number must reside in contiguous locations, with up to 256 locations. The minimum number of bytes in a line of SQTP should be the Word size of the memory. It can be a multiple of the Word size, up to 256 bytes. -
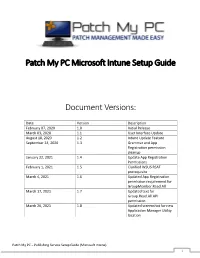
Patch My PC Microsoft Intune Setup Guide Document Versions
Patch My PC Microsoft Intune Setup Guide Document Versions: Date Version Description February 07, 2020 1.0 Initial Release March 03, 2020 1.1 User Interface Update August 18, 2020 1.2 Intune Update Feature September 24, 2020 1.3 Grammar and App Registration permission cleanup January 22, 2021 1.4 Update App Registration Permissions February 1, 2021 1.5 Clarified WSUS RSAT prerequisite March 4, 2021 1.6 Updated App Registration permission requirement for GroupMember.Read.All March 17, 2021 1.7 Updated text for Group.Read.All API permission March 26, 2021 1.8 Updated screenshot for new Application Manager Utility location Patch My PC – Publishing Service Setup Guide (Microsoft Intune) 1 System Requirements: • Microsoft .NET Framework 4.5 • Supported Operating Systems o Windows Server 2008 o Windows Server 2012 o Windows Server 2016 o Windows Server 2019 o Windows 10 (x64) – Microsoft Intune only Prerequisites: • WSUS Remote Server Administration Tools (RSAT) to be installed Download the latest MSI installer of the publishing service using the following URL: https://patchmypc.com/publishing- service-download Start the installation by double- clicking the downloaded MSI. Note: Depending on user account control settings, you may need to run an elevated command prompt and launch the MSI from the command prompt. Click Next in the Welcome Wizard Click Next in the Installation Folder Dialog Optionally, you can change the installation folder by clicking Browse… Click Install on the Ready to Install dialog. Note: if user-account control is enabled, you will receive a prompt “Do you want to allow this app to make changes to your device?” Click Yes on this prompt to allow installation Patch My PC – Publishing Service Setup Guide (Microsoft Intune) 2 If you are configuring the product for Intune Win32 application publishing only, you can check Enable Microsoft Intune standalone mode When this option is enabled, prerequisite checks related to WSUS and Configuration Manager are skipped. -

DR DOS for the Zfx86
DR DOS for the ZFx86 Cost Effective, Reliable, Rapid Deployment of Embedded Systems w DR DOS on the ZFx86 gets products to market quickly at the lowest development and ownership cost. w Thousands of compatible applications, drivers and utilities available free or at minimal cost. w Full documentation available. DR DOS 7.03 Key Features of DR DOS Online Manual - DRDOS is supplied with a complete The ideal embedded DOS system, online manual that contains detailed information about all designed for out-of-the-box of the features of the operating system including the basic implementation into ROM or Flash commands, and the advanced utilities. It also has online ROM with tools and associated help available for all its commands. documents available in the DRDOS Memory Management - Memory management features OEM Documentation Kit. include a set of device drivers and commands that enable w 100% MS-DOS 6.22 compatible.. you to manage memory efficiently and make as much memory as possible available to your applications. w Comprehensive DOS utility set DOS Protected Mode Services - DOS Protected Mode w Multitasking, with API for developers Services (DPMS) interface allows specially-implemented w DPMS memory manager in addition to DPMI device drivers and TSRs to operate in extended memory. w Stacker disk compression This makes more memory within the first megabyte w NWCACHE - disk caching program available to applications and other conventionally-written drivers and TSRs. Both Stacker* (the disk compression w EMM386 memory manager program), and NWCACHE (the disk cache) use DPMS. w DOS Protected Mode Services (DPMS) Disk Compression - The disk compression component w Multitasking enables you to store more information by compressing the w DR-DOS provides a full multitasking environment data.