Deployment of NAT Vs. Ipv6 in Bittorrent
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-

N2N: a Layer Two Peer-To-Peer VPN
N2N: A Layer Two Peer-to-Peer VPN Luca Deri1, Richard Andrews2 ntop.org, Pisa, Italy1 Symstream Technologies, Melbourne, Australia2 {deri, andrews}@ntop.org Abstract. The Internet was originally designed as a flat data network delivering a multitude of protocols and services between equal peers. Currently, after an explosive growth fostered by enormous and heterogeneous economic interests, it has become a constrained network severely enforcing client-server communication where addressing plans, packet routing, security policies and users’ reachability are almost entirely managed and limited by access providers. From the user’s perspective, the Internet is not an open transport system, but rather a telephony-like communication medium for content consumption. This paper describes the design and implementation of a new type of peer-to- peer virtual private network that can allow users to overcome some of these limitations. N2N users can create and manage their own secure and geographically distributed overlay network without the need for central administration, typical of most virtual private network systems. Keywords: Virtual private network, peer-to-peer, network overlay. 1. Motivation and Scope of Work Irony pervades many pages of history, and computing history is no exception. Once personal computing had won the market battle against mainframe-based computing, the commercial evolution of the Internet in the nineties stepped the computing world back to a substantially rigid client-server scheme. While it is true that the today’s Internet serves as a good transport system for supplying a plethora of data interchange services, virtually all of them are delivered by a client-server model, whether they are centralised or distributed, pay-per-use or virtually free [1]. -

NAT Traversal About
NAT Traversal About Some difficulties have been encountered with devices that have poor NAT support. FreeSWITCH goes to great lengths to repair broken NAT support in phones and gateway devices. In order to aid FreeSWITCH in traversing NAT please see the External profile page. Some routers offer an Application Layer Gateway feature which can prevent FreeSWITCH NAT traversal from working. See the ALG page for more information, including how to disable it. Using STUN to aid in NAT Traversal STUN is a method to allow an end host (i.e. phone) to discover its public IP address if it is located behind a NAT . Using this method requires a STUN server on the public internet and a client on the phone. The phone's STUN client queries the STUN server for it's own public IP and transmits the information it has received in it's connection information in the SIP packets it sends to the SIP server. Enable and configure STUN settings on your phone in order correctly to report your phone's contact information to FreeSWITCH when registering. Unfortunately, not all phones have a properly working STUN client. STUN servers This site contains a list of public STUN servers: https://gist.github.com/zziuni/3741933 stun.freeswitch.org is never guaranteed to be up and running so use it in production at your own risk. There are several open source projects to run your own STUN server, e.g. STUNTMAN Using FreeSWITCH built-in methods to aid in NAT Traversal nat-options-ping This parameter causes FreeSWITCH to regularly (every 20 - 40s) send an OPTIONS packet to NATed registered endpoints in order to keep the port on the clients firewall open. -

Digital Fountain Erasure-Recovery in Bittorrent
UNIVERSITÀ DEGLI STUDI DI BERGAMO Facoltà di Ingegneria Corso di Laurea Specialistica in Ingegneria Informatica Classe n. 35/S – Sistemi Informatici Digital Fountain Erasure Recovery in BitTorrent: integration and security issues Relatore: Chiar.mo Prof. Stefano Paraboschi Correlatore: Chiar.mo Prof. Andrea Lorenzo Vitali Tesi di Laurea Specialistica Michele BOLOGNA Matricola n. 56108 ANNO ACCADEMICO 2007 / 2008 This thesis has been written, typeset and prepared using LATEX 2". Printed on December 5, 2008. Alla mia famiglia “Would you tell me, please, which way I ought to go from here?” “That depends a good deal on where you want to get to,” said the Cat. “I don’t much care where —” said Alice. “Then it doesn’t matter which way you go,” said the Cat. “— so long as I get somewhere,” Alice added as an explanation. “Oh, you’re sure to do that,” said the Cat, “if you only walk enough.” Lewis Carroll Alice in Wonderland Acknowledgments (in Italian) Ci sono molte persone che mi hanno aiutato durante lo svolgimento di questo lavoro. Il primo ringraziamento va ai proff. Stefano Paraboschi e Andrea Vitali per la disponibilità, la competenza, i consigli, la pazienza e l’aiuto tecnico che mi hanno saputo dare. Grazie di avermi dato la maggior parte delle idee che sono poi confluite nella mia tesi. Un sentito ringraziamento anche a Andrea Rota e Ruben Villa per l’aiuto e i chiarimenti che mi hanno gentilmente fornito. Vorrei ringraziare STMicroelectronics, ed in particolare il gruppo Advanced System Technology, per avermi offerto le infrastrutture, gli spa- zi e tutto il necessario per svolgere al meglio il mio periodo di tirocinio. -

NAT and NAT Traversal Lecturer: Andreas Müller [email protected]
NAT and NAT Traversal lecturer: Andreas Müller [email protected] NetworkIN2097 - MasterSecurity, Course WS 2008/09, Computer Chapter Networks, 9 WS 2009/2010 39 NAT: Network Address Translation Problem: shortage of IPv4 addresses . more and more devices . only 32bit address field Idea: local network uses just one IP address as far as outside world is concerned: . range of addresses not needed from ISP: just one IP address for all devices . can change addresses of devices in local network without notifying outside world . can change ISP without changing addresses of devices in local network . devices inside local net not explicitly addressable, visible by outside world (a security plus). NetworkIN2097 - MasterSecurity, Course WS 2008/09, Computer Chapter Networks, 9 WS 2009/2010 40 NAT: Network Address (and Port) Translation rest of local network Internet (e.g., home network) 10.0.0/24 10.0.0.1 10.0.0.4 10.0.0.2 138.76.29.7 10.0.0.3 All datagrams leaving local Datagrams with source or network have same single source destination in this network NAT IP address: 138.76.29.7, have 10.0.0/24 address for different source port numbers source, destination (as usual) NetworkIN2097 - MasterSecurity, Course WS 2008/09, Computer Chapter Networks, 9 WS 2009/2010 41 NAT: Network Address Translation Implementation: NAT router must: . outgoing datagrams: replace (source IP address, port #) of every outgoing datagram to (NAT IP address, new port #) . remote clients/servers will respond using (NAT IP address, new port #) as destination addr. remember (in NAT translation table) every (source IP address, port #) to (NAT IP address, new port #) translation pair -> we have to maintain a state in the NAT . -

You Are Not Welcome Among Us: Pirates and the State
International Journal of Communication 9(2015), 890–908 1932–8036/20150005 You Are Not Welcome Among Us: Pirates and the State JESSICA L. BEYER University of Washington, USA FENWICK MCKELVEY1 Concordia University, Canada In a historical review focused on digital piracy, we explore the relationship between hacker politics and the state. We distinguish between two core aspects of piracy—the challenge to property rights and the challenge to state power—and argue that digital piracy should be considered more broadly as a challenge to the authority of the state. We trace generations of peer-to-peer networking, showing that digital piracy is a key component in the development of a political platform that advocates for a set of ideals grounded in collaborative culture, nonhierarchical organization, and a reliance on the network. We assert that this politics expresses itself in a philosophy that was formed together with the development of the state-evading forms of communication that perpetuate unmanageable networks. Keywords: pirates, information politics, intellectual property, state networks Introduction Digital piracy is most frequently framed as a challenge to property rights or as theft. This framing is not incorrect, but it overemphasizes intellectual property regimes and, in doing so, underemphasizes the broader political challenge posed by digital pirates. In fact, digital pirates and broader “hacker culture” are part of a political challenge to the state, as well as a challenge to property rights regimes. This challenge is articulated in terms of contributory culture, in contrast to the commodification and enclosures of capitalist culture; as nonhierarchical, in contrast to the strict hierarchies of the modern state; and as faith in the potential of a seemingly uncontrollable communication technology that makes all of this possible, in contrast to a fear of the potential chaos that unsurveilled spaces can bring. -

Torrent Download Audio Tv Torrent Downloads Proxy – Best Torrent Downloads Unblocked Alternative | Mirror Sites
torrent download audio tv Torrent Downloads Proxy – Best Torrent Downloads Unblocked Alternative | Mirror Sites. We all know that the torrent sites banned over the last few days and users are facing problems like browser bans, ISP bans across the country. At present, the site is banned in the UK, India and so many countries because of court orders. Luckily, Torrent downloads professional staff and different torrent lovers are offering Torrent downloads proxy and mirror sites for us with newest proxies. These websites will have the same records, appearance, and functions just like the original one. Torrent Downloads: Torrent Downloads is one of the popular torrent sites which come in the list of top 10. This site is providing you the latest TV shows, Movies, Music, Games, Software, Anime, Books and so on for many years. The content of this site is very unique where you will get the latest movies, software within a few minutes. That’s why many of the users are still visit this site on a daily basis to download for free of cost. Torrent Downloads Proxy and Mirrors list: These Torrent Downloads Proxy/Mirror sites are used in such countries where it is not banned yet. So, If you couldn’t get right of entry to Torrent Downloads, with the assist of Torrent Downloads proxy/mirror websites , you’ll usually be able to get right of entry to your favorite torrent website, Torrent Downloads. Your Internet Service Provider and Government can track your browsing Activity! So, hide your IP Address with a VPN! Torrent Downloads Proxy/Mirror Sites: https://freeproxy.io/ https://sitenable.top/ https://sitenable.ch/ https://filesdownloader.com/ https://sitenable.pw/ https://sitenable.co/ https://torrentdownloads.unblockall.org/ https://torrentdownloads.unblocker.cc/ https://torrentdownloads.unblocker.win/ https://torrentdownloads.immunicity.cab/ How to Download Torrent Downloads Movies securely? Using torrents is illegal in some countries. -
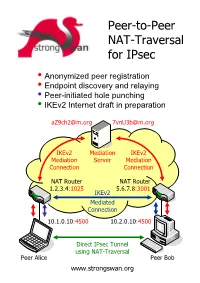
Peer-To-Peer NAT-Traversal for Ipsec
Peer-to-Peer NAT-Traversal for IPsec y Anonymized peer registration y Endpoint discovery and relaying y Peer-initiated hole punching y IKEv2 Internet draft in preparation [email protected] [email protected] IKEv2 Mediation IKEv2 Mediation Server Mediation Connection Connection NAT Router NAT Router 1.2.3.4:1025 5.6.7.8:3001 IKEv2 Mediated Connection 10.1.0.10:4500 10.2.0.10:4500 Direct IPsec Tunnel using NAT-Traversal Peer Alice Peer Bob www.strongswan.org The double NAT case - where punching holes counts! ● You are selling automation systems all over the world. In order to save on travel expenses you want to remotely diagnose and update your deployed systems via the Internet. But security counts – thus IPsec is a must! Unfortunately both you and your customer are behind NAT routers so that no direct VPN connection is possible. You are helplessly blocked! ● You own an apartment at home, in the mountains or even abroad. You want to remotely control the heating or your sophisticated intrusion detection system via ADSL or Cable access. But since you and your apartment are separated by two NAT routers your are helplessly blocked. How it works! ● Two peers want to set up a direct IPsec tunnel using the established NAT traversal mechanism of encapsulating ESP packets in UDP datagrams. Unfortunately they cannot achieve this by themselves because neither host is seen from the Internet under the standard IKE NAT-T port 4500. Therefore both peers need to set up a mediation connection with an IKEv2 mediation server. In order to prevent unsolicited connection attempts by foreign peers, the mediation connections use randomized pseudonyms as IKE peer identities. -

Problems of Ipsec in Combination with NAT and Their Solutions
Problems of IPsec in Combination with NAT and Their Solutions Alexander Heinlein Abstract As the Internet becomes more and more a part of our daily life it also evolves as an at- tractive target for security attacks, often countered by Internet Protocol Security (IPsec) to establish virtual private networks (VPNs), if secure data communication is a primary objective. Then again, to provide Internet access for hosts inside Local Area Networks, a public IP address shared among all peers is often used, achieved by Network Address Translation (NAT) deployment. IPsec, however, is incompatible with NAT, leading to a variety of problems when using both in combination. Connection establishments origi- nating from the outside are blocked and NAT, as it modifies the outer IP header, breaks IPsec’s security mechanisms. In the following we analyze problems of NAT in combination with IPsec and multiple approaches to solve them. 1 Introduction The current TCP/IP protocols originate from a time where security was not a great concern. As the traditional Internet Protocol (IP) does not provide any guarantees on delivery, the receiver cannot detect whether the sender is the same one as recorded in the protocol header or if the packet was modified during transport. Moreover an attacker may also easily replay IP packets or read sensitive information out of them. In contrast, today, as the Internet becomes more and more a part of our everyday life, a more security aware protocol is needed. To fill this gap the Internet Engineering Task Force (IETF) worked on a new standard for securing IP, called Internet Protocol Security (IPsec). -

The Impact of Network Address Translation on Peer-To-Peer Live Video Streaming Systems
The Impact of Network Address Translation on Peer-to-Peer Live Video Streaming Systems by Zhonghua Wei M.Sc., University of London, 2006 B.Eng., Beijing Univ. of Posts and Telecommunications, 2005 A Thesis Submitted in Partial Fulfillment of the Requirements for the Degree of MASTER OF SCIENCE in the Department of Computer Science c Zhonghua Wei, 2011 University of Victoria All rights reserved. This thesis may not be reproduced in whole or in part, by photocopying or other means, without the permission of the author. ii The Impact of Network Address Translation on Peer-to-Peer Live Video Streaming Systems by Zhonghua Wei M.Sc., University of London, 2006 B.Eng., Beijing Univ. of Posts and Telecommunications, 2005 Supervisory Committee Dr. Jianping Pan, Supervisor (Department of Computer Science) Dr. Kui Wu, Departmental Member (Department of Computer Science) iii Supervisory Committee Dr. Jianping Pan, Supervisor (Department of Computer Science) Dr. Kui Wu, Departmental Member (Department of Computer Science) ABSTRACT Video streaming over the Internet can be very difficult under the traditional client-server model. Peer-to-peer (P2P) systems, in which each participating peer contributes its upload bandwidth to other peers while it downloads data, have been successful in file-sharing applications, and they appear to be promising in delivering video contents, too. However, the existence of network address translation (NAT) is always considered as a challenge to peer-to-peer systems. NAT has been a practical solution to the Internet Protocol version 4 (IPv4) address exhaustion problem, as it reduces the usage of IP addresses by allowing multiple private hosts to share a single public IP address, but NAT can degrade the performance of a peer-to-peer system as it limits the direction of connectivity. -

Developing P2P Protocols Across NAT Girish Venkatachalam
Developing P2P Protocols across NAT Girish Venkatachalam Abstract Hole punching is a possible solution to solving the NAT problem for P2P protocols. Network address translators (NATs) are something every software engineer has heard of, not to mention networking professionals. NAT has become as ubiquitous as the Cisco router in networking terms. Fundamentally, a NAT device allows multiple machines to communicate with the Internet using a single globally unique IP address, effectively solving the scarce IPv4 address space problem. Though not a long-term solution, as originally envisaged in 1994, for better or worse, NAT technology is here to stay, even when IPv6 addresses become common. This is partly because IPv6 has to coexist with IPv4, and one of the ways to achieve that is by using NAT technology. This article is not so much a description of how a NAT works. There already is an excellent article on this subject by Geoff Huston (see the on-line Resources). It is quite comprehensive, though plenty of other resources are available on the Internet as well. This article discusses a possible solution to solving the NAT problem for P2P protocols. What Is Wrong with NAT? NAT breaks the Internet more than it makes it. I may sound harsh here, but ask any peer-to-peer application developer, especially the VoIP folks, and they will tell you why. For instance, you never can do Web hosting behind a NAT device. At least, not without sufficient tweaking. Not only that, you cannot run any service such as FTP or rsync or any public service through a NAT device. -

Connectivity Properties of Mainline Bittorrent DHT Nodes
IEEE P2P'09 - Sept. 9-11, 2009 Connectivity Properties of Mainline BitTorrent DHT Nodes Raul Jimenez Flutra Osmani Bj¨orn Knutsson Royal Institute of Technology (KTH) ICT/TSLAB Stockholm, Sweden {rauljc, flutrao, bkn}@kth.se Abstract raises some concerns about the scalability and resilience of the technology. The birth and evolution of Peer-to-Peer (P2P) protocols Our work is part of the P2P-Next[1] project, which is have, for the most part, been about peer discovery. Napster, supported by many partners including the EBU2 who claims one of the first P2P protocols, was basically FTP/HTTP to have more than 650 million viewers weekly. In the face plus a way of finding hosts willing to send you the file. Since of such load, scalability and resilience become vital compo- then, both the transfer and peer discovery mechanisms have nents of the underlying technology. improved, but only recently have we seen a real push to In BitTorrent, content is distributed in terms of objects, completely decentralized peer discovery to increase scal- consisting of one or more files, and these objects are de- ability and resilience. scribed by a torrent-file. The clients (peers)participatingin Most such efforts are based on Distributed Hash Tables the distribution of one such object form a swarm. (DHTs), with Kademlia being a popular choice of DHT im- Aswarmiscoordinatedbyatracker,whichkeepstrack plementation. While sound in theory, and performing well of every peer in the swarm. In order to join a swarm, a peer in simulators and testbeds, the real-world performance of- must contact the tracker, which registers the new peer and ten falls short of expectations. -
Kickass Proxy List Documentation Release Latest
Kickass Proxy List Documentation Release latest Apr 12, 2021 CONTENTS 1 Kickass Proxies 3 2 Top Kickass Proxy and Mirror Sites from UnblockNinja:5 3 Is Kickass blocked in my country?7 4 How to unblock KickassTorrents9 i ii Kickass Proxy List Documentation, Release latest The Kickass site is the best source where you can download Multi category torrents. If your ISP blocks Kickass or for some reason cannot access it, just go to one of the Kickass proxy sites article. You will get instant access through the Kickass mirror so that you can download all the multimedia content you need. CONTENTS 1 Kickass Proxy List Documentation, Release latest 2 CONTENTS CHAPTER ONE KICKASS PROXIES Perhaps the easiest way to access the site is through Kickass proxies. A proxy server is a server that acts as an intermediary for requests from clients looking for resources from other servers. When accessing Kickass through a proxy server, external observers only see that you are connected to the proxy server and do not see that the proxy server is transmitting Kickass data to you. Kickass proxies are sometimes mistaken for Kickass mirrors. Mirror 1337x is just a clone of the source site with a different domain name and servers. The Kickass proxy server, on the other hand, is a separate site that makes it easy to connect to the original Kickass, as well as often to other websites. In practice, it doesn’t matter if you connect to Kickass through a proxy server or use an Kickass mirror, as they both provide about the same degree of privacy.