How to Apply Patches Against the Vulnerability CVE-2019-0708 (“Bluekeep”)
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-

2020 Sonicwall Cyber Threat Report
2020 SONICWALL CYBER THREAT REPORT sonicwall.com I @sonicwall TABLE OF CONTENTS 3 A NOTE FROM BILL 4 CYBERCRIMINAL INC. 11 2019 GLOBAL CYBERATTACK TRENDS 12 INSIDE THE SONICWALL CAPTURE LABS THREAT NETWORK 13 KEY FINDINGS FROM 2019 13 SECURITY ADVANCES 14 CRIMINAL ADVANCES 15 FASTER IDENTIFICATION OF ‘NEVER-BEFORE-SEEN’ MALWARE 16 TOP 10 CVES EXPLOITED IN 2019 19 ADVANCEMENTS IN DEEP MEMORY INSPECTION 23 MOMENTUM OF PERIMETER-LESS SECURITY 24 PHISHING DOWN FOR THIRD STRAIGHT YEAR 25 CRYPTOJACKING CRUMBLES 27 RANSOMWARE TARGETS STATE, PROVINCIAL & LOCAL GOVERNMENTS 31 FILELESS MALWARE SPIKES IN Q3 32 ENCRYPTED THREATS GROWING CONSISTENTLY 34 IOT ATTACK VOLUME RISING 35 WEB APP ATTACKS DOUBLE IN 2019 37 PREPARING FOR WHAT’S NEXT 38 ABOUT SONICWALL 2 A NOTE FROM BILL The boundaries of your digital empire are In response, SonicWall and our Capture Labs limitless. What was once a finite and threat research team work tirelessly to arm defendable space is now a boundless organizations, enterprises, governments and territory — a vast, sprawling footprint of businesses with actionable threat devices, apps, appliances, servers, intelligence to stay ahead in the global cyber networks, clouds and users. arms race. For the cybercriminals, it’s more lawless And part of that dedication starts now with than ever. Despite the best intentions of the 2020 SonicWall Cyber Threat Report, government agencies, law enforcement and which provides critical threat intelligence to oversight groups, the current cyber threat help you better understand how landscape is more agile than ever before. cybercriminals think — and be fully prepared for what they’ll do next. -

Adaptive Android Kernel Live Patching
Adaptive Android Kernel Live Patching Yue Chen Yulong Zhang Zhi Wang Liangzhao Xia Florida State University Baidu X-Lab Florida State University Baidu X-Lab Chenfu Bao Tao Wei Baidu X-Lab Baidu X-Lab Abstract apps contain sensitive personal data, such as bank ac- counts, mobile payments, private messages, and social Android kernel vulnerabilities pose a serious threat to network data. Even TrustZone, widely used as the se- user security and privacy. They allow attackers to take cure keystore and digital rights management in Android, full control over victim devices, install malicious and un- is under serious threat since the compromised kernel en- wanted apps, and maintain persistent control. Unfortu- ables the attacker to inject malicious payloads into Trust- nately, most Android devices are never timely updated Zone [42, 43]. Therefore, Android kernel vulnerabilities to protect their users from kernel exploits. Recent An- pose a serious threat to user privacy and security. droid malware even has built-in kernel exploits to take Tremendous efforts have been put into finding (and ex- advantage of this large window of vulnerability. An ef- ploiting) Android kernel vulnerabilities by both white- fective solution to this problem must be adaptable to lots hat and black-hat researchers, as evidenced by the sig- of (out-of-date) devices, quickly deployable, and secure nificant increase of kernel vulnerabilities disclosed in from misuse. However, the fragmented Android ecosys- Android Security Bulletin [3] in recent years. In ad- tem makes this a complex and challenging task. dition, many kernel vulnerabilities/exploits are publicly To address that, we systematically studied 1;139 An- available but never reported to Google or the vendors, droid kernels and all the recent critical Android ker- let alone patched (e.g., exploits in Android rooting nel vulnerabilities. -

Igloosec Security Report
Monthly Security Report 2019 June Cyber attack prevention and detection automation using CTI & vulnerability assessment result CVE-2019-0708 (BlueKeep) Advanced social engineering hacking technique, aimed at people. This report is based on the data collected through the SIEM solution at IGLOO Security’s Security Operation Center (SOC). IGLOO Security continuously strives to achieve a 24/7 safe cyber environment throughout the year. -2 - MONTHLY SECURITY REPORT 201906 Cover Story 1. Monthly Security Issues - Monthly security issues 2. IGLOO Statistics - Monthly Attack Service and Trend Analysis - Detailed Analysis According to Different Patterns 3. SIEM Guide (SPiDER TM V5.x) 4. Tech Note - CVE-2019-0708 (BlueKeep) 5. Special Column - Advanced social engineering hacking techniques, aimed at people 6. Focus On IGLOO Security - Participation in the 2019 Defense Security Conference Information Security Product Exhibition -3 - MONTHLY SECURITY REPORT 201906 CHAPTER 1 Monthly Security Issues 1. Monthly security issues -4 - MONTHLY SECURITY REPORT 201906 1 Monthly Security Issues ‘For the next generation’… Gand Crab Ransomware creator announces discontinuation of Gand Crab • GandCrab Ransomware creator has earned $ 2 billion. Now attracting attention by announcing that it will no longer produce a service-oriented Ransomware (RaaS). • GandCrab Ransomware, which was first unveiled in January 2018, has recently appeared in the 5.2 version and produced a lot of damage. • According to the blip computer, the creator has invested in legitimate businesses by cashing in revenues from the company. The creator are expected to delete the entire cryptographic key along with the release of the Ransomware, and victims who want to retrieve the files encrypted by Gandcrab are prompted to pay for the decryption quickly. -
Digital Vision Network 5000 Series BCM Motherboard BIOS Upgrade
Digital Vision Network 5000 Series BCM™ Motherboard BIOS Upgrade Instructions October, 2011 24-10129-128 Rev. – Copyright 2011 Johnson Controls, Inc. All Rights Reserved (805) 522-5555 www.johnsoncontrols.com No part of this document may be reproduced without the prior permission of Johnson Controls, Inc. Cardkey P2000, BadgeMaster, and Metasys are trademarks of Johnson Controls, Inc. All other company and product names are trademarks or registered trademarks of their respective owners. These instructions are supplemental. Some times they are supplemental to other manufacturer’s documentation. Never discard other manufacturer’s documentation. Publications from Johnson Controls, Inc. are not intended to duplicate nor replace other manufacturer’s documentation. Due to continuous development of our products, the information in this document is subject to change without notice. Johnson Controls, Inc. shall not be liable for errors contained herein or for incidental or consequential damages in connection with furnishing or use of this material. Contents of this publication may be preliminary and/or may be changed at any time without any obligation to notify anyone of such revision or change, and shall not be regarded as a warranty. If this document is translated from the original English version by Johnson Controls, Inc., all reasonable endeavors will be used to ensure the accuracy of translation. Johnson Controls, Inc. shall not be liable for any translation errors contained herein or for incidental or consequential damages in connection -
Guide to Enterprise Patch Management Technologies
NIST Special Publication 800-40 Revision 3 Guide to Enterprise Patch Management Technologies Murugiah Souppaya Karen Scarfone C O M P U T E R S E C U R I T Y NIST Special Publication 800-40 Revision 3 Guide to Enterprise Patch Management Technologies Murugiah Souppaya Computer Security Division Information Technology Laboratory Karen Scarfone Scarfone Cybersecurity Clifton, VA July 2013 U.S. Department of Commerce Penny Pritzker, Secretary National Institute of Standards and Technology Patrick D. Gallagher, Under Secretary of Commerce for Standards and Technology and Director Authority This publication has been developed by NIST to further its statutory responsibilities under the Federal Information Security Management Act (FISMA), Public Law (P.L.) 107-347. NIST is responsible for developing information security standards and guidelines, including minimum requirements for Federal information systems, but such standards and guidelines shall not apply to national security systems without the express approval of appropriate Federal officials exercising policy authority over such systems. This guideline is consistent with the requirements of the Office of Management and Budget (OMB) Circular A-130, Section 8b(3), Securing Agency Information Systems, as analyzed in Circular A- 130, Appendix IV: Analysis of Key Sections. Supplemental information is provided in Circular A-130, Appendix III, Security of Federal Automated Information Resources. Nothing in this publication should be taken to contradict the standards and guidelines made mandatory and binding on Federal agencies by the Secretary of Commerce under statutory authority. Nor should these guidelines be interpreted as altering or superseding the existing authorities of the Secretary of Commerce, Director of the OMB, or any other Federal official. -

Sonicwall Cyber Threat Report a Note from Bill
2 0 SONICWALL 2 1 CYBER THREAT REPORT Cyber threat intelligence for navigating the new business reality sonicwall.com | @sonicwall Table of Contents A Note From Bill 3 Ransomware by Region 37 Introduction 4 Ransomware by Signature 38 2020 Global Cyberattack Trends 5 Ransomware by Industry 42 Top Data Exposures of 2020 6 Intrusion Attempts 44 Power Shifts Changing Future of Cybersecurity 7 Top Intrusion Attacks 46 Published CVEs Nearly Triple Since 2015 10 Intrusion Attempts by Region 47 Top 8 CVEs Exploited in 2020 10 Capture ATP and RTDMI 48 2020 Zero-Day Vulnerabilities 12 ‘Never-Before-Seen’ Malware 50 COVID Threats: Exploiting a Pandemic 13 Malicious Office and PDF Files 51 COVID-19-Related Attacks by Industry 14 Cryptojacking 52 2020’s Biggest Cybersecurity Events 16 Cryptojacking Attempts by Industry 56 Key Findings from 2020 19 IoT Malware Attacks 58 Malware Attempts 21 A Year in IoT Malware Attacks 62 Malware Spread 22 IoT Malware Attacks by Industry 64 Malware Risk by Country 24 Non-Standard Ports 66 Malware Spread by Country 30 Conclusion 67 Malware Attempts by Industry 31 About the SonicWall Capture Labs Threat Network 68 Encrypted Attacks 33 Featured Threat Researchers 69 Ransomware 35 About SonicWall 70 2 | 2021 SonicWall Cyber Threat Report A Note From Bill The World Economic Forum asked respondents in a recent Cyber-resiliency means expanding your focus beyond study which dangers will pose the largest threat to the world simply securing your network and your data, to ensuring over the next two years. business continuity in the event of an attack or some other Unsurprisingly for a pandemic year, “infectious diseases” unforeseen event. -

Android 10 OS Update Instruction for Family of Products on SDM660
Android 10 OS Update Instruction for Family of Products on SDM660 1 Contents 1. A/B (Seamless) OS Update implementation on SDM660 devices ................................................................................................... 2 2. How AB system is different to Non-AB system ............................................................................................................................... 3 3. Android AB Mode for OS Update .................................................................................................................................................... 4 4. Recovery Mode for OS Update ........................................................................................................................................................ 4 5. Reset Packages and special recovery packages ................................................................................................................................ 4 6. OS Upgrade and Downgrade ............................................................................................................................................................ 5 7. OS Upgrade and Downgrade via EMMs .......................................................................................................................................... 6 8. AB Streaming Update ....................................................................................................................................................................... 7 9. User Notification for Full OTA package -

Catalogue Formations (PDF)
Page 2 L’intégrale VERISAFE Véritable cursus de formation en Cybersécurité : 120 heures de formation, 850 vidéos & 4200 slides La cybercriminalité fait peser une menace grandissante sur tous les organismes (privés ou pu- blics) et sur chaque citoyen. Pour lutter efficacement contre ce fléau, il est important de bien comprendre le phénomène et de l’anticiper. Illustrée par des exemples réels, cette formation détaille le monde cybercriminel (organisation, acteurs, motivations, techniques d’attaques, moyens financiers et humains,…). Elle présente également les acteurs et les dispositifs juri- diques pour lutter contre les cybercriminels au niveau national comme au niveau international. Face une véritable pénurie en matière de compétences en matière de sécurité Cloud, la certifi- cation CCSK de la Cloud Security Alliance est devenue la certification internationale la plus re- cherchée et se place désormais à la 1er place en matière de rémunération (Source : Certificate Magazine). Cette formation intensive a été spécialement conçue pour préparer et obtenir cette certification en 30 jours. Ransomware, espionnage économique ou scientifique, fuites de données à caractère person- nel,… le nombre de cyberattaques ne cesse d’augmenter en France et dans le monde. La ques- tion n’est donc pas de savoir si votre organisme sera attaqué mais plutôt comment répondre efficacement à ces attaques. Cette formation répond à toutes les préoccupations actuelles et dresse l’état de l’art en matière de cybersécurité à destination des entreprises et des adminis- trations. C’est la formation Cybersécurité le plus suivie en France avec 18 sessions en présentiel et plus de 316 participants en 2019. Cette formation intensive permet d’acquérir toutes les compétences nécessaires pour devenir un professionnel de la cybersécurité reconnu sur le marché. -
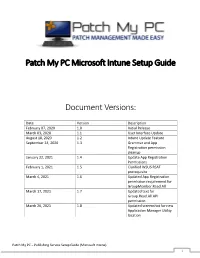
Patch My PC Microsoft Intune Setup Guide Document Versions
Patch My PC Microsoft Intune Setup Guide Document Versions: Date Version Description February 07, 2020 1.0 Initial Release March 03, 2020 1.1 User Interface Update August 18, 2020 1.2 Intune Update Feature September 24, 2020 1.3 Grammar and App Registration permission cleanup January 22, 2021 1.4 Update App Registration Permissions February 1, 2021 1.5 Clarified WSUS RSAT prerequisite March 4, 2021 1.6 Updated App Registration permission requirement for GroupMember.Read.All March 17, 2021 1.7 Updated text for Group.Read.All API permission March 26, 2021 1.8 Updated screenshot for new Application Manager Utility location Patch My PC – Publishing Service Setup Guide (Microsoft Intune) 1 System Requirements: • Microsoft .NET Framework 4.5 • Supported Operating Systems o Windows Server 2008 o Windows Server 2012 o Windows Server 2016 o Windows Server 2019 o Windows 10 (x64) – Microsoft Intune only Prerequisites: • WSUS Remote Server Administration Tools (RSAT) to be installed Download the latest MSI installer of the publishing service using the following URL: https://patchmypc.com/publishing- service-download Start the installation by double- clicking the downloaded MSI. Note: Depending on user account control settings, you may need to run an elevated command prompt and launch the MSI from the command prompt. Click Next in the Welcome Wizard Click Next in the Installation Folder Dialog Optionally, you can change the installation folder by clicking Browse… Click Install on the Ready to Install dialog. Note: if user-account control is enabled, you will receive a prompt “Do you want to allow this app to make changes to your device?” Click Yes on this prompt to allow installation Patch My PC – Publishing Service Setup Guide (Microsoft Intune) 2 If you are configuring the product for Intune Win32 application publishing only, you can check Enable Microsoft Intune standalone mode When this option is enabled, prerequisite checks related to WSUS and Configuration Manager are skipped. -

Patch Management for Redhat Enterprise Linux
Patch Management for RedHat Enterprise Linux Supported Versions BigFix provides coverage for RedHat updates on the following platforms: • RedHat Enterprise Linux 5 • RedHat Enterprise Linux 4 • RedHat Enterprise Linux 3 BigFix covers the following RedHat updates on these platforms: • RedHat Security Advisories • RedHat Bug Fix Advisories • RedHat Enhancement Advisories Patching using Fixlet Messages To deploy patches from the BigFix Console: 1. On the Fixlet messages tab, sort by Site. Choose the Site Patches for RedHat Enterprise Linux. 2. Double-click on the Fixlet message you want to deploy. (In this example, the Fixlet message is RHSA-2007:0992 - Libpng Security Update - Red Hat Enterprise 3.0.) The Fixlet window opens. For more information about setting options using the tabs in the Fixlet window, consult the Console Operators Guide. 3. Select the appropriate Action link. © 2007 by BigFix, Inc. BigFix Patch Management for RedHat Enterprise Linux Page 2 A Take Action window opens. For more information about setting options using the tabs in the Take Action dialog box, consult the Console Operators Guide. 4. Click OK, and enter your Private Key Password when asked. Using the Download Cacher The Download Cacher is designed to automatically download and cache RedHat RPM packages to facilitate deployment of RedHat Enterprise Linux Fixlet messages. Running the Download Cacher Task BigFix provides a Task for running the Download Cacher Tool for RedHat Enterprise Linux. 1. From the Tasks tab, choose Run Download Cacher Tool – Red Hat Enterprise. The Task window opens. © 2007 by BigFix, Inc. BigFix Patch Management for RedHat Enterprise Linux Page 3 2. Select the appropriate Actiont link. -

Mind the Gap: Dissecting the Android Patch Gap | Ben Schlabs
Mind the Gap – Dissecting the Android patch gap Ben Schlabs <[email protected]> SRLabs Template v12 Corporate Design 2016 Allow us to take you on two intertwined journeys This talk in a nutshell § Wanted to understand how fully-maintained Android phones can be exploited Research § Found surprisingly large patch gaps for many Android vendors journey – some of these are already being closed § Also found Android exploitation to be unexpectedly difficult § Wanted to check thousands of firmwares for the presence of Das Logo Horizontal hundreds of patches — Pos / Neg Engineering § Developed and scaled a rather unique analysis method journey § Created an app for your own analysis 2 3 Android patching is a known-hard problem Patching challenges Patch ecosystems § Computer OS vendors regularly issue patches OS vendor § Users “only” have to confirm the installation of § Microsoft OS patches Patching is hard these patches § Apple Endpoints & severs to start with § Still, enterprises consider regular patching § Linux distro among the most effortful security tasks § “The moBile ecosystem’s diversity […] OS Chipset Phone Android contriButes to security update complexity and vendor vendor vendor phones inconsistency.” – FTC report, March 2018 [1] The nature of Telco § Das Logo HorizontalAndroid makes Patches are handed down a long chain of — Pos / Negpatching so typically four parties Before reaching the user much more § Only some devices get patched (2016: 17% [2]). difficult We focus our research on these “fully patched” phones Our research question – -
Bluekeep Vulnerability
Monthly Cybersecurity Newsletter June 2019 Issue Enterprise Security and Risk Management Office (ESRMO) From the Desk of the State Chief Risk Officer – Maria Thompson BlueKeep Vulnerability The National Security Agency (NSA) has released a cybersecurity advisory for a vulnerability (CVE-2019-0708) called “BlueKeep” that affects several old versions of the Microsoft Windows operating system. The BlueKeep vulnerability allows for an unauthenticated attacker to connect to a vulnerable system using the Remote Desktop Protocol (RDP) – formerly known as Terminal Services – and send specially crafted requests without user interaction. An attacker who successfully exploits this vulnerability could then install programs; view, change, or delete data; or create new accounts with full user rights on the vulnerable machine. Microsoft warns that the vulnerability is also “wormable,” meaning it can potentially spread from system to system without user interaction. The “BlueKeep” vulnerability is present in Windows 7, Windows XP, and Server 2003 and 2008. Windows 8 and Windows 10 are not currently vulnerable. Although Microsoft has issued a patch for this vulnerability, potentially millions of machines are still vulnerable. Microsoft strongly recommends installing the updates for this vulnerability as soon as possible, after appropriate testing. The update addresses the vulnerability by correcting how Remote Desktop Services (RDS) handles connection requests. In addition to installing the patch, the following steps may also help reduce the risk of this vulnerability. • Disable RDS if it is not required. Disabling unused and unneeded services reduces exposure to security vulnerabilities. • Enable Network Level Authentication (NLA) on systems running supported Windows editions. With NLA turned on, an attacker would first need to authenticate to RDS with a valid account on the target system before exploiting the vulnerability.