Ansible Documentation Release 1.7
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-

DIRECTOR's REPORT September 21, 2017
DIRECTOR’S REPORT September 21, 2017 SUMMER PROGRAMMING The 2017 Summer Reading Club (SRC), Read Up! Rise Up! by Design, utilized key aspects of the design thinking methodology in the development of the SRC program curriculum. Design thinking, as it relates to program development, seeks to identify creative solutions to problems by utilizing solution-based strategies. In an ideal setting these creative strategies ultimately result in a constructive resolution to an identified problem or challenge. The design thinking methodology is used in a variety of disciplines i.e. urban planning, web development, education etc. Programming content focused on S.T.R.E.A.M (Science, Technology, Reading, Writing, Engineering, Arts and Math) related subjects. Throughout the summer program participants participated in variety of enrichment activities that promoted creative thinking, problem solving, reading, writing and other forms of creative expression. Summer Reading Club registration began May 15th, 2017 with the contest and associated programming continuing for 9 weeks (June 5th – August 5th). 10,156 students registered for this year’s SRC with 5,286 participants completing. The 2017 completion rate continued its upward trend with 52% of all participants completing the program. The Cleveland Public Library received generous financial and in-kind support from the Friends of the Cleveland Public Library Foundation, The Cleveland Museum of Art, The City of Cleveland, Cleveland Fire Department, Cleveland Metropolitan School District, United Way of Greater Cleveland, Greater Cleveland Food Bank, KPMG, Mitchell’s Ice Cream, McDonalds, and Georgio’s Pizza. The Library was also the recipient of multiple book grants that enabled children to receive free books for participating in the program. -

Not for Sale Not for Sale
chapter 3 Installing Fedora Now comes the moment of truth. You’ve done the homework, figured out how you want to install your copy of Fedora, and you’re ready to go. This chapter won’t disappoint you. Its sole goal is to walk you through the installation process using the Anaconda graphical installer. Along the way, you will: ■ Discover how to explore Fedora—without installing it. ■ Choose which option will be best for you, installing Fedora alone or along- side another operating system. ■ Journey step by step through the installation process. ■ Create one or more users for your Fedora machine. Try Before You Buy © Cengage Learning. All rights reserved. No distribution allowed without express authorization. This section may leave you scratching your head and wondering why you just went through all of the preparation in Chapter 2. Be patient, there’s a method to this madness. All spins of Fedora are currently available to users as a LiveCD version. “LiveCD” is the label for operating systems that can be booted and run right from the CD itself—without installing on your computer’s hard drive. 41 Game Developing GWX Not For Sale Not For Sale 42 Chapter 3 ■ Installing Fedora This means that when you insert your Fedora CD into the disc drive and restart your computer, Fedora will automatically begin running on your computer without putting on any new files or touching pre-existing data on your machine. Fedora just starts up and runs. So why, you ask, should I bother installing Fedora at all? I can just run it from the CD. -

TECHNICAL STANDARDS a Standards Validation Committee of Industry Representatives and Educators Reviewed and Updated These Standards on December 11, 2017
SOFTWARE AND APP DESIGN 15.1200.40 TECHNICAL STANDARDS A Standards Validation Committee of industry representatives and educators reviewed and updated these standards on December 11, 2017. Completion of the program prepares students to meet the requirements of one or more industry certification: Cybersecurity Fundamentals Certificate, Oracle Certified Associate, Java SE 8 Programmer, Certified Internet Web (CIW) - JavaScript Specialist, CompTIA A+, CompTIA IT Fundamentals, CSX Cybersecurity Fundamentals Certificate, and Microsoft Technology Associate (MTA). The Arizona Career and Technical Education Quality Commission, the validating entity for the Arizona Skills Standards Assessment System, endorsed these standards on January 25, 2018. Note: Arizona’s Professional Skills are taught as an integral part of the Software and App Design program. The Technical Skills Assessment for Software and App Design is available SY2020-2021. Note: In this document i.e. explains or clarifies the content and e.g. provides examples of the content that must be taught. STANDARD 1.0 APPLY PROBLEM-SOLVING AND CRITICAL THINKING SKILLS 1.1 Establish objectives and outcomes for a task 1.2 Explain the process of decomposing a large programming problem into smaller, more manageable procedures 1.3 Explain “visualizing” as a problem-solving technique prior to writing code 1.4 Describe problem-solving and troubleshooting strategies applicable to software development STANDARD 2.0 RECOGNIZE SECURITY ISSUES 2.1 Identify common computer threats (e.g., viruses, phishing, -
Debian Installation Manual
Powered by Universal Speech Solutions LLC MRCP Deb Installation Manual Administrator Guide Revision: 70 Created: February 7, 2015 Last updated: March 15, 2021 Author: Arsen Chaloyan Powered by Universal Speech Solutions LLC | Overview 1 Table of Contents 1 Overview ............................................................................................................................................... 3 1.1 Applicable Versions ............................................................................................................ 3 1.2 Supported Distributions ...................................................................................................... 3 1.3 Authentication ..................................................................................................................... 3 2 Installing Deb Packages Using Apt-Get ............................................................................................... 4 2.1 Repository Configuration ................................................................................................... 4 2.2 GnuPG Key ......................................................................................................................... 4 2.3 Repository Update .............................................................................................................. 4 2.4 UniMRCP Client Installation .............................................................................................. 5 2.5 UniMRCP Server Installation ............................................................................................ -
Release Notes for Fedora 22
Fedora 22 Release Notes Release Notes for Fedora 22 Edited by The Fedora Docs Team Copyright © 2015 Fedora Project Contributors. The text of and illustrations in this document are licensed by Red Hat under a Creative Commons Attribution–Share Alike 3.0 Unported license ("CC-BY-SA"). An explanation of CC-BY-SA is available at http://creativecommons.org/licenses/by-sa/3.0/. The original authors of this document, and Red Hat, designate the Fedora Project as the "Attribution Party" for purposes of CC-BY-SA. In accordance with CC-BY-SA, if you distribute this document or an adaptation of it, you must provide the URL for the original version. Red Hat, as the licensor of this document, waives the right to enforce, and agrees not to assert, Section 4d of CC-BY-SA to the fullest extent permitted by applicable law. Red Hat, Red Hat Enterprise Linux, the Shadowman logo, JBoss, MetaMatrix, Fedora, the Infinity Logo, and RHCE are trademarks of Red Hat, Inc., registered in the United States and other countries. For guidelines on the permitted uses of the Fedora trademarks, refer to https:// fedoraproject.org/wiki/Legal:Trademark_guidelines. Linux® is the registered trademark of Linus Torvalds in the United States and other countries. Java® is a registered trademark of Oracle and/or its affiliates. XFS® is a trademark of Silicon Graphics International Corp. or its subsidiaries in the United States and/or other countries. MySQL® is a registered trademark of MySQL AB in the United States, the European Union and other countries. All other trademarks are the property of their respective owners. -
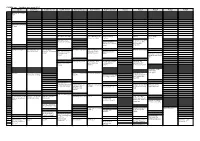
FOSDEM 2017 Schedule
FOSDEM 2017 - Saturday 2017-02-04 (1/9) Janson K.1.105 (La H.2215 (Ferrer) H.1301 (Cornil) H.1302 (Depage) H.1308 (Rolin) H.1309 (Van Rijn) H.2111 H.2213 H.2214 H.3227 H.3228 Fontaine)… 09:30 Welcome to FOSDEM 2017 09:45 10:00 Kubernetes on the road to GIFEE 10:15 10:30 Welcome to the Legal Python Winding Itself MySQL & Friends Opening Intro to Graph … Around Datacubes Devroom databases Free/open source Portability of containers software and drones Optimizing MySQL across diverse HPC 10:45 without SQL or touching resources with my.cnf Singularity Welcome! 11:00 Software Heritage The Veripeditus AR Let's talk about The State of OpenJDK MSS - Software for The birth of HPC Cuba Game Framework hardware: The POWER Make your Corporate planning research Applying profilers to of open. CLA easy to use, aircraft missions MySQL Using graph databases please! 11:15 in popular open source CMSs 11:30 Jockeying the Jigsaw The power of duck Instrumenting plugins Optimized and Mixed License FOSS typing and linear for Performance reproducible HPC Projects algrebra Schema Software deployment 11:45 Incremental Graph Queries with 12:00 CloudABI LoRaWAN for exploring Open J9 - The Next Free It's time for datetime Reproducible HPC openCypher the Internet of Things Java VM sysbench 1.0: teaching Software Installation on an old dog new tricks Cray Systems with EasyBuild 12:15 Making License 12:30 Compliance Easy: Step Diagnosing Issues in Webpush notifications Putting Your Jobs Under Twitter Streaming by Open Source Step. Java Apps using for Kinto Introducing gh-ost the Microscope using Graph with Gephi Thermostat and OGRT Byteman. -
Red Hat Enterprise Linux 8 Security Hardening
Red Hat Enterprise Linux 8 Security hardening Securing Red Hat Enterprise Linux 8 Last Updated: 2021-09-06 Red Hat Enterprise Linux 8 Security hardening Securing Red Hat Enterprise Linux 8 Legal Notice Copyright © 2021 Red Hat, Inc. The text of and illustrations in this document are licensed by Red Hat under a Creative Commons Attribution–Share Alike 3.0 Unported license ("CC-BY-SA"). An explanation of CC-BY-SA is available at http://creativecommons.org/licenses/by-sa/3.0/ . In accordance with CC-BY-SA, if you distribute this document or an adaptation of it, you must provide the URL for the original version. Red Hat, as the licensor of this document, waives the right to enforce, and agrees not to assert, Section 4d of CC-BY-SA to the fullest extent permitted by applicable law. Red Hat, Red Hat Enterprise Linux, the Shadowman logo, the Red Hat logo, JBoss, OpenShift, Fedora, the Infinity logo, and RHCE are trademarks of Red Hat, Inc., registered in the United States and other countries. Linux ® is the registered trademark of Linus Torvalds in the United States and other countries. Java ® is a registered trademark of Oracle and/or its affiliates. XFS ® is a trademark of Silicon Graphics International Corp. or its subsidiaries in the United States and/or other countries. MySQL ® is a registered trademark of MySQL AB in the United States, the European Union and other countries. Node.js ® is an official trademark of Joyent. Red Hat is not formally related to or endorsed by the official Joyent Node.js open source or commercial project. -

Hydra: a Declarative Approach to Continuous Integration1
Hydra: A Declarative Approach to Continuous Integration1 Eelco Dolstra, Eelco Visser Department of Software Technology, Faculty of Electrical Engineering, Mathematics and Computer Science (EWI), Delft University of Technology, The Netherlands Abstract There are many tools to support continuous integration: the process of automatically and con- tinuously building a project from a version management repository. However, they do not have good support for variability in the build environment: dependencies such as compilers, libraries or testing tools must typically be installed manually on all machines on which automated builds are performed. In this paper we present Hydra, a continuous build tool based on Nix, a package manager that has a purely functional language for describing package build actions and their dependencies. This allows the build environment for projects to be produced automatically and deterministically, and so significantly reduces the effort to maintain a continuous integration en- vironment. 1. Introduction Hydra is a tool for continuous integration testing and software release that uses a purely func- tional language to describe build jobs and their dependencies. Continuous integration (Fowler and Foemmel 2006) is a simple technique to improve the quality of the software development process. An automated system continuously or periodically checks out the source code of a project, builds it, runs tests, and produces reports for the developers. Thus, various errors that might accidentally be committed into the code base are automatically caught. Such a system allows more in-depth testing than what developers could feasibly do manually: • Portability testing: The software may need to be built and tested on many different plat- forms. -

Solaris 10 End of Life
Solaris 10 end of life Continue Oracle Solaris 10 has had an amazing OS update, including ground features such as zones (Solaris containers), FSS, Services, Dynamic Tracking (against live production operating systems without impact), and logical domains. These features have been imitated in the market (imitation is the best form of flattery!) like all good things, they have to come to an end. Sun Microsystems was acquired by Oracle and eventually, the largest OS known to the industry, needs to be updated. Oracle has set a retirement date of January 2021. Oracle indicated that Solaris 10 systems would need to raise support costs. Oracle has never provided migratory tools to facilitate migration from Solaris 10 to Solaris 11, so migration to Solaris has been slow. In September 2019, Oracle decided that extended support for Solaris 10 without an additional financial penalty would be delayed until 2024! Well its March 1 is just a reminder that Oracle Solaris 10 is getting the end of life regarding support if you accept extended support from Oracle. Combined with the fact gdpR should take effect on May 25, 2018 you want to make sure that you are either upgraded to Solaris 11.3 or have taken extended support to obtain any patches for security issues. For more information on tanningix releases and support dates of old and new follow this link ×Sestive to abort the Unix Error Operating System originally developed by Sun Microsystems SolarisDeveloperSun Microsystems (acquired by Oracle Corporation in 2009)Written inC, C'OSUnixWorking StateCurrentSource ModelMixedInitial release1992; 28 years ago (1992-06)Last release11.4 / August 28, 2018; 2 years ago (2018-08-28)Marketing targetServer, PlatformsCurrent: SPARC, x86-64 Former: IA-32, PowerPCKernel typeMonolithic with dynamically downloadable modulesDefault user interface GNOME-2-LicenseVariousOfficial websitewww.oracle.com/solaris Solaris is the own operating system Of Unix, originally developed by Sunsystems. -

Puppet Offers a Free, Reliable and Cross Flavor Option for Remote Enterprise Computer Management
This material is based on work supported by the National Science Foundation under Grant No. 0802551 Any opinions, findings, and conclusions or recommendations expressed in this material are those of the author (s) and do not necessarily reflect the views of the National Science Foundation C4L8S1 System administrators are constantly challenged when managing large enterprise systems using Linux-based operating systems. Administrators need to know a variety of command line differentiations, dependency variations, and support options to support the various computers systems in use. Puppet offers a free, reliable and cross flavor option for remote enterprise computer management. This lesson will introduce you to the Puppet AdministrativeU the tool and provide you with a basic overview on how to use Puppet. Lab activities will provide you with hands-on experience with the Puppet application and assignments and discussion activities will increase your learning on this subject. Understanding Puppet is important because of its ability to manage enterprise systems. Students hoping to become Linux Administrators must gain mastery of enterprise management tools like Puppet to improve efficiency and productivity. C4L8S2 You should know what will be expected of you when you complete this lesson. These expectations are presented as objectives. Objectives are short statements of expectations that tell you what you must be able to do, perform, learn, or adjust after reviewing the lesson. Lesson Objective: U the Given five computers that need to be configured, -
Salt Documentation Release 2014.7.6
Salt Documentation Release 2014.7.6 SaltStack, Inc. May 19, 2015 Contents 1 Introduction to Salt 1 1.1 e 30 second summary ........................................... 1 1.2 Simplicity ................................................... 1 1.3 Parallel execution ............................................... 1 1.4 Building on proven technology ....................................... 2 1.5 Python client interface ............................................ 2 1.6 Fast, flexible, scalable ............................................. 2 1.7 Open ...................................................... 2 1.8 Salt Community ................................................ 2 1.9 Mailing List .................................................. 2 1.10 IRC ....................................................... 3 1.11 Follow on Github ............................................... 3 1.12 Blogs ...................................................... 3 1.13 Example Salt States .............................................. 3 1.14 Follow on ohloh ................................................ 3 1.15 Other community links ............................................ 4 1.16 Hack the Source ................................................ 4 2 Installation 5 2.1 ick Install .................................................. 5 2.2 Platform-specific Installation Instructions ................................. 5 2.3 Dependencies ................................................. 26 2.4 Optional Dependencies ............................................ 27 2.5 Upgrading -

Urpmi.Addmedia
Todo lo que siempre quisiste saber sobre urpmi pero nunca te atreviste a preguntarlo Todo lo que siempre quisiste saber sobre urpmi pero nunca te atreviste a preguntarlo Traducido por Willy Walker de http://mandrake.vmlinuz.ca/bin/view/Main/UsingUrpmi Descargalo en PDF Otros recursos para aprender sobre urpmi Urpmi es una importante herramienta para todos los usuarios de Mandriva. Tomate tiempo para aprender utilizarlo. Esta página te da una descripción de las opciones más comúnmente usadas. Debajo están otros recursos con una información más detallada sobre urpmi: ● http://www.urpmi.org/ : Página de buena documentación de urpmi en Francés y en Inglés. ● Páginas man: comprueba las páginas man para todas las opciones. Ésas son la fuente más actualizada de información. Junto a una introducción muy básica, esta página intenta cubrir lo qué no se cubre en las dos fuentes antedichas de información. Asumimos que sabes utilizar una página man y que has leído la página antedicha. Una vez que lo hayas hecho así, vuelve a esta página: hay más información sobre problemas no tan obvios que puede no funcionarte. Usando urpmi Lista rápida de tareas comunes Comando Que te dice urpmq -i xxx.rpm Información del programa urpmq -il xxx.rpm Información y los archivos que instala urpmq --changelog xxx.rpm changelog (cambios) urpmq -R xxx.rpm Que requiere este rpm urpmf ruta/a/archivo Que rpm proporciona este archivo rpm -q --whatprovides ruta/a/ similar a urpmf, pero trabaja con ambos hdlist.cz y synthesis.hdlist.cz archivo urpmi.update updates Actualizaciones disponibles desde sus fuentes de actualización Actualizaciones disponibles desde todas las fuentes urpmi (puede urpmc necesitar urpmi a urpmc primero) urpmq --list-media Lista los repositorios que tienes Todo lo que siempre quisiste saber sobre urpmi pero nunca te atreviste a preguntarlo Comando Que hace urpme xxxx Elimina el rpm (y dependencias) Muestra todos los rpms que coinciden con esta cadena.