Manual Gentoo Linux AMD64
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-

Alpine Linux: Minimalistická Distribuce Nejen Na Server
Alpine Linux: minimalistická distribuce nejen na server Petr Krčmář 5. března 2017 Uvedené dílo (s výjimkou obrázků) podléhá licenci Creative Commons Uveďte autora 3.0 Česko. Petr Krčmář (Root.cz, vpsFree.cz) Alpine Linux: minimalistická distribuce nejen na server 5. března 2017 1 / 19 Petr Krčmář (Root.cz, vpsFree.cz) Alpine Linux: minimalistická distribuce nejen na server 5. března 2017 2 / 19 Prezentace už teď na webu https://www.petrkrcmar.cz Petr Krčmář (Root.cz, vpsFree.cz) Alpine Linux: minimalistická distribuce nejen na server 5. března 2017 3 / 19 Historie Alpine první verze 2006 původně jako fork LEAF (Linux Embedded Appliance Framework) to je zase fork LRP (Linux Router Project) = disketové distribuce vývojáři ale chtěli jít za hranici disket zůstala jednoduchost a přehlednost umožnilo to nasazení mimo jednoduché firewally dnes plnohodnotná distribuce stále umí běžet z RAM nezávislá, nekomerční Petr Krčmář (Root.cz, vpsFree.cz) Alpine Linux: minimalistická distribuce nejen na server 5. března 2017 4 / 19 K čemu se hodí? velká plnohodnotná distribuce embedded zařízení (síťové prvky) firewally routery ústředny VoIP servery a kontejnery ale i na desktop (Xfce, Gnome) Petr Krčmář (Root.cz, vpsFree.cz) Alpine Linux: minimalistická distribuce nejen na server 5. března 2017 5 / 19 Motto Small. Simple. Secure. Petr Krčmář (Root.cz, vpsFree.cz) Alpine Linux: minimalistická distribuce nejen na server 5. března 2017 6 / 19 Small. instalace v kontejneru jen 8 MB, 260 souborů 16 balíčků, jen 6 z jiných projektů instalace do virtuálu 53 MB, 1222 souborů 26 balíčků plná instalace na železo 302 MB, 4686 souborů 27 balíčků hodně jaderných modulů Petr Krčmář (Root.cz, vpsFree.cz) Alpine Linux: minimalistická distribuce nejen na server 5. -

Ubuntu Kung Fu
Prepared exclusively for Alison Tyler Download at Boykma.Com What readers are saying about Ubuntu Kung Fu Ubuntu Kung Fu is excellent. The tips are fun and the hope of discov- ering hidden gems makes it a worthwhile task. John Southern Former editor of Linux Magazine I enjoyed Ubuntu Kung Fu and learned some new things. I would rec- ommend this book—nice tips and a lot of fun to be had. Carthik Sharma Creator of the Ubuntu Blog (http://ubuntu.wordpress.com) Wow! There are some great tips here! I have used Ubuntu since April 2005, starting with version 5.04. I found much in this book to inspire me and to teach me, and it answered lingering questions I didn’t know I had. The book is a good resource that I will gladly recommend to both newcomers and veteran users. Matthew Helmke Administrator, Ubuntu Forums Ubuntu Kung Fu is a fantastic compendium of useful, uncommon Ubuntu knowledge. Eric Hewitt Consultant, LiveLogic, LLC Prepared exclusively for Alison Tyler Download at Boykma.Com Ubuntu Kung Fu Tips, Tricks, Hints, and Hacks Keir Thomas The Pragmatic Bookshelf Raleigh, North Carolina Dallas, Texas Prepared exclusively for Alison Tyler Download at Boykma.Com Many of the designations used by manufacturers and sellers to distinguish their prod- ucts are claimed as trademarks. Where those designations appear in this book, and The Pragmatic Programmers, LLC was aware of a trademark claim, the designations have been printed in initial capital letters or in all capitals. The Pragmatic Starter Kit, The Pragmatic Programmer, Pragmatic Programming, Pragmatic Bookshelf and the linking g device are trademarks of The Pragmatic Programmers, LLC. -

Wicd をやめる. Dd でなく最初から Flash Mathlibre を作る参考
tk:2017-04-27 [cc111] 2019/05/08 13*03 cc111 メモ.txt.zip,mathlibre2018-vmware.txt.zip mathlibre 2017 を flash memory へインストールするとネットワークがうまく動作しない場合がある. /sbin/ifconfig -a するとデタラメな IP アドレスが設定されていたり、何も設定されていなかったりする. そこで wicd を捨てる ことにしたらどうやらうまくいってる模様. sudo su - /etc/init.d/wicd stop ifconfig eth0 10.1.204.222 netmask 255.255.0.0 broadcast 10.1.255.255 route add -net 10.1.0.0 metric 1 netmask 255.255.0.0 eth0 route add -net default gw 10.1.254.254 上のアドレスは環境にあわせて適宜変更. cd /etc/init.d mkdir ../init.d.available mv wicd ../init.d.availabe で野蛮に wicd が起動しないようにしておく. search math.kobe-u.ac.jp domain math.kobe-u.ac.jp nameserver 10.1.254.3 と /etc/resolv.conf に書く. apt-get update apt-get install network-manager /etc/init.d/network-manager start 再起動. だめならもう一度再起動. wicd を消してしまうのもいいかも. apt-get remove wick apt-get remove python-wicd トラブルシュート. 1. IP address? /sbin/ifconfig -a でうまく動いてるか確認. 2. ps ps axuww | grep Net でそもそもネットワークマネージャが動いてるか確認. http://cc111.math.kobe-u.ac.jp/doku.php?id=tk:2017-04-27 1 / 2 ページ tk:2017-04-27 [cc111] 2019/05/08 13*03 3. root になって, ping www.math.kobe-u.ac.jp 4. 名前を知らないといわれる. /etc/resolv.conf の内容は正しい? 5. network unreachable になる. route で見える routing table は正しい? その他メモ. 1. 時刻設定 sudo su - ; ntpdate ntp.nict.jp 2. nslookup apt-get dnsutils obsolete な nslookup を使いたいとき. 3. caps lock と ctrl の入れ替えは tray の左グループの右. 4. nm-applet は apt-get install network-manager-gnome 5. todo, wicd を tray から消したい. network-manager の control panel を表示したい. -

Introduction Use Runit with Traditional Init (Sysvinit)
2021/07/26 19:10 (UTC) 1/12 Runit Runit Introduction runit is a UNIX init scheme with service supervision. It is a cross-platform Unix init scheme with service supervision, a replacement for sysvinit, and other init schemes and supervision that are used with the traditional init. runit is compatible with djb's daemontools. In Unix-based computer operating systems, init (short for initialization) is the first process started during booting of the computer system. Init is a daemon process that continues running until the system is shut down. Slackware comes with its own legacy init (/sbin/init) from the sysvinit package, that used to be included in almost all other major Linux distributions. The init daemon (or its replacement) is characterised by Process ID 1 (PID 1). To read on the benefits of runit, see here: http://smarden.org/runit/benefits.html * Unless otherwise stated, all commands in this article are to be run by root. Use runit with traditional init (sysvinit) runit is not provided by Slackware, but a SlackBuild is maintained on https://slackbuilds.org/. It does not have any dependencies. As we do not want yet to replace init with runit, run the slackbuild with CONFIG=no: CONFIG=no ./runit.SlackBuild Then install the resulting package and proceed as follows: mkdir /etc/runit/ /service/ cp -a /usr/doc/runit-*/etc/2 /etc/runit/ /sbin/runsvdir-start & Starting via rc.local For a typical Slackware-stlyle service, you can edit /etc/rc.d/rc.local file if [ -x /sbin/runsvdir-start ]; then /sbin/runsvdir-start & fi and then edit write /etc/rc.d/rc.local_shutdown #!/bin/sh SlackDocs - https://docs.slackware.com/ Last update: 2020/05/06 08:08 (UTC) howtos:slackware_admin:runit https://docs.slackware.com/howtos:slackware_admin:runit RUNIT=x$( /sbin/pidof runsvdir ) if [ "$RUNIT" != x ]; then kill $RUNIT fi Then give rc.local_shutdown executive permission: chmod +x /etc/rc.d/rc.local_shutdown and reboot Starting via inittab (supervised) Remove the entries in /etc/rc.d/rc.local and /etc/rc.d/rc.local_shutdown described above. -

Introduction to Gentoo Linux
Introduction to Gentoo Linux Ulrich Müller Developer and Council member, Gentoo Linux <[email protected]> Institut für Kernphysik, Universität Mainz <[email protected]> Seminar “Learn Linux the hard way”, Mainz, 2012-10-23 Ulrich Müller (Gentoo Linux) Introduction to Gentoo Linux Mainz 2012 1 / 35 Table of contents 1 History 2 Why Gentoo? 3 Compile everything? – Differences to other distros 4 Gentoo features 5 Gentoo as metadistribution 6 Organisation of the Gentoo project 7 Example of developer’s work Ulrich Müller (Gentoo Linux) Introduction to Gentoo Linux Mainz 2012 2 / 35 /"dZEntu:/ Pygoscelis papua Fastest swimming penguin Source: Wikimedia Commons License: CC-BY-SA-2.5, Attribution: Stan Shebs Ulrich Müller (Gentoo Linux) Introduction to Gentoo Linux Mainz 2012 3 / 35 How I came to Gentoo UNIX since 1987 (V7 on Perkin-Elmer 3220, later Ultrix, OSF/1, etc.) GNU/Linux since 1995 (Slackware, then S.u.S.E.) Switched to Gentoo in January 2004 Developer since April 2007 Council Mai 2009–June 2010 and since July 2011 Projects: GNU Emacs, eselect, PMS, QA Ulrich Müller (Gentoo Linux) Introduction to Gentoo Linux Mainz 2012 4 / 35 Overview Based on GNU/Linux, FreeBSD, etc. Source-based metadistribution Can be optimised and customised for any purpose Extremely configurable, portable, easy-to-maintain Active all-volunteer developer community Social contract GPL, LGPL, or other OSI-approved licenses Will never depend on non-free software Is and will always remain Free Software Commitment to giving back to the FLOSS community, e.g. submit bugs -

Unit V Algorithm for Booting the UNIX System
Unit V Algorithm for booting the UNIX system : As we’ve noted, the boot process begins when the instructions stored in the computer’s permanent, nonvolatile memory (referred to colloquially as the BIOS, ROM,NVRAM, and so on) are executed. This storage location for the initial boot instructions is generically referred to as firmware (in contrast to “software,” but reflecting the fact that the instructions constitute a program[2]). These instructions are executed automatically when the power is turned on or the system is reset, although the exact sequence of events may vary according to the values of stored parameters.[3] The firmware instructions may also begin executing in response to a command entered on the system console (as we’ll see in a bit). However they are initiated, these instructions are used to locate and start up the system’s boot program , which in turn starts the Unix operating system. The boot program is stored in a standard location on a bootable device. For a normal boot from disk, for example, the boot program might be located in block 0 of the root disk or, less commonly, in a special partition on the root disk. In the same way, the boot program may be the second file on a bootable tape or in a designated location on a remote file server in the case of a network boot of a diskless workstation. There is usually more than one bootable device on a system. The firmware program may include logic for selecting the device to boot from, often in the form of a list of potential devices to examine. -
Functional Package and Configuration Management with GNU Guix
Functional Package and Configuration Management with GNU Guix David Thompson Wednesday, January 20th, 2016 About me GNU project volunteer GNU Guile user and contributor since 2012 GNU Guix contributor since 2013 Day job: Ruby + JavaScript web development / “DevOps” 2 Overview • Problems with application packaging and deployment • Intro to functional package and configuration management • Towards the future • How you can help 3 User autonomy and control It is becoming increasingly difficult to have control over your own computing: • GNU/Linux package managers not meeting user needs • Self-hosting web applications requires too much time and effort • Growing number of projects recommend installation via curl | sudo bash 1 or otherwise avoid using system package managers • Users unable to verify that a given binary corresponds to the source code 1http://curlpipesh.tumblr.com/ 4 User autonomy and control “Debian and other distributions are going to be that thing you run Docker on, little more.” 2 2“ownCloud and distribution packaging” http://lwn.net/Articles/670566/ 5 User autonomy and control This is very bad for desktop users and system administrators alike. We must regain control! 6 What’s wrong with Apt/Yum/Pacman/etc.? Global state (/usr) that prevents multiple versions of a package from coexisting. Non-atomic installation, removal, upgrade of software. No way to roll back. Nondeterminstic package builds and maintainer-uploaded binaries. (though this is changing!) Reliance on pre-built binaries provided by a single point of trust. Requires superuser privileges. 7 The problem is bigger Proliferation of language-specific package managers and binary bundles that complicate secure system maintenance. -
The Magpi Magazine Is Published by Raspberry Pi (Trading) Ltd., 30 Station Road, Cambridge, CB1 2JH
GET A CAMERA MODULE FIRST WITH YOUR OFFICIAL RASPBERRY PI MAGAZINE Issue 45 Issue • May 2016 May The official Raspberry Pi magazine Issue 45 May 2016 raspberrypi.org/magpi PICTURE PERFECT The NEW Raspberry Pi Camera Module is here! REPLICATE A PI ZERO- AN ASTRO PI POWERED EXPERIMENT RAILWAY Make your own Pi takes a Dorset humidity sensor model railway to the next level MAKE NEOPIXEL HACKING WITH DINOSAURS ELECTRONICS Jurassic Park, eat Build impressive your heart out! costume effects BUILD AN IOT THREE NEW PI GAMES TO PLAY THERMOMETER From GameMaker: Studio And share your data online Also inside: THE BEST ARCA PI > CODER DOJO GETS A MASSIVE BOOST *E MACHINES Our top 10 magpi.cc > TAKE AMAZING PICTURES OF THE MOON retro gaming > THE ORACLE WEATHER STATION ARRIVES Issue 45 • May 2016 • £5.99 arcade cabinets > THE LATEST GADGETS REVIEWED & RATED powered by Pi 05 THE ONLY PI MAGAZINE WRITTEN BY THE READERS, FOR THE READERS 9772051998001 Welcome PROUD WELCOME TO SUPPORTERS OF: THE OFFICIAL PI MAGAZINE! he Raspberry Pi Camera Module is one of the T most popular add-ons for the Raspberry Pi. Released in 2013, it made use of the previously dormant CSI connector, spawned a whole new genre of amazing Raspberry Pi projects, and has since found itself everywhere from the depths of the ocean to the dizzy heights of the International Space Station. Its 5MP sensor was equivalent to the kind of standard cameras you’d find on smartphones of the time, but since three years is an eternity in technology, Raspberry Pi have just released a shiny new update. -
Wifi Penetration Wireless Communication and Computer/Network Forensics Terms
Wifi Penetration Wireless Communication and Computer/Network Forensics Terms ● Skiddy(Derogatory): Variant of "Script Kiddy". ● Hacker(Derogatory):One who builds something. ● Cracker(Derogatory):One who breaks something. ● Penetration Test: Method of evaluating Computer/Network security by simulating an attack. ● Penetration Tester: One who implements different attack tools to asses Computer/Network vulnerabilities. Wifi / WLAN / Wireless Spectrum depends on what country you're in. America uses 14 channels designated in 2.4 ghz spaced 5mhz apart. Wireless Encryption ● Wired Equivalent Privacy(WEP): The least form of security. FBI Demonstrated 3 minute hack in 2005. 40 bit or 104 bit encryption Key. ● Wifi Protected Acces(WPA): Replace WEP, and use of Temporal Key Integrity Protocol (TKIP). Implements 128 bit encryption. ● (WPA2): Successor to WPA, replaces TKIP with Counter Cypher Mode Protocol (CCMP). Also Implements different algorithm Advanced Encryption Standard (AES), 256 bit encryption. Wireless Antennas Omnidirectional: Common "Rubber Ducky" antenna. Directional: Common "Flat-Panel" or a variant of "Pringles-Can" antenna. Sniper Directional: Common "Yagi" antenna, resembles antennas commonly found on house roofs. http://vimeo.com/8826952 Wiretapping/Eavesdropping laws ● CA Eavesdropping and Wiretapping law: PENAL CODE SECTION 630-638 ● CA PENAL CODE SECTION 484-502.9 ● Google was fined $7 million because a rogue engineer was using a penetration tool called "Kismet". Kismet is similar to aircrack, but is scripted to automatically break into networks when a password is found. It also provides a google maps view. ● It is perfectly legal to perform penetration testing techniques on your own equipment. It is also perfectly legal to be in promiscuous mode, i.e. -

Happy Birthday Linux
25 Jahre Linux! Am Anfang war der Quellcode Entstehungsgeschichte und Werdegang von Linux Entwicklung und Diversifizierung der Distributionen Der Wert von Linux oder: „Wat nix kost, dat is och nix.“ Andreas Klein ORR 2016 1 Am Anfang war der Quellcode (70er) ● 1969, Ken Thompson u. Dennis Ritchie erstellen die erste Version von Unix in Assembler. ● Von 1969-1971 entwickeln sie gemeinsam die Programmiersprache B. ● Ab 1971 erweiterte in erster Linie Dennis Ritchie B, um weitere Elemente und nannte sie Anfangs NB (new B). ● 1973 waren die Erweiterungen soweit gediehen, das er die stark verbesserte Sprache C nannte (Brian W. Kernighan hat ebenfalls maßgeblich dazu beigetragen). //Unix=25 PCs ● Bis 1974 war das gesamte Betriebssystem UNIX vollständig in C implementiert und wurde mit einem C-Compiler kostenfrei an verschiedene Universitäten verteilt. ● 1978 wurden bereits über 600 Computer mit dem UNIX-Betriebssystemen betrieben. ● Das aufblühende Zeitalter der Computerisierung der 70er Jahre war geprägt vom regen und freien Austausch von Programmen und dessen zugrunde liegenden Ideen. Sinnvoller Weise tauschte man diese als Quellcode untereinander aus. ● 1979 wurde von AT&T die letzte UNIX-Version 7, mit freiem Quellcode veröffentlicht. Andreas Klein ORR 2016 2 Am Anfang war der Quellcode (80er) ● 1980 – 1983 AT&T sowie zahlreiche andere Unternehmen beginnen mit der Kommerzialisierung von UNIX, durch Koppelung an stark beschränkenden Lizenzen und Geheimhaltung des zugrunde liegenden Quelltextes. ● Richard Stallman kündigt am 27. September 1983 in den Newsgroups net.unix-wizards und net.usoft das GNU-Projekt an. ● Am 5. Januar 1984 begann Stallman offiziell mit der Arbeit am GNU-Projekt, nachdem er seine Stelle am MIT gekündigt hatte. -
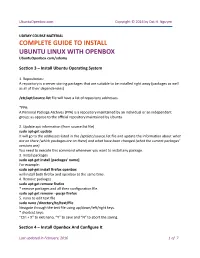
COMPLETE GUIDE to INSTALL UBUNTU LINUX with OPENBOX Ubuntuopenbox.Com/Udemy
UbuntuOpenbox.com Copyright © 2016 by Dat H. Nguyen UDEMY COURSE MATERIAL COMPLETE GUIDE TO INSTALL UBUNTU LINUX WITH OPENBOX UbuntuOpenbox.com/udemy Section 3 – Install Ubuntu Operating System 1. Repositories: A repository is a server storing packages that are suitable to be installed right away (packages as well as all of their dependencies) /etc/apt/source.list file will have a list of repository addresses. *PPA: A Personal Package Archives (PPA) is a repository maintained by an individual or an independent group; as oppose to the official repository maintained by Ubuntu. 2. Update apt information (from source.list file) sudo apt-get update It will go to the addresses listed in the /apt/etc/source.list file and update the information about what are on there (which packages are on there) and what have been changed (what the current packages’ versions are). You need to execute this command whenever you want to install any package. 3. Install packages sudo apt-get install [packages' name] For example: sudo apt-get install firefox openbox will install both firefox and openbox at the same time. 4. Remove packages sudo apt-get remove firefox * remove packages and all their configuration file. sudo apt-get remove --purge firefox 5. nano to edit text file sudo nano /directory/to/text/file Navigate through the text file using up/down/left/right keys. * shortcut keys: “Ctrl + X” to exit nano, “Y” to save and “N” to abort the saving. Section 4 – Install Openbox And Configure It Last updated in February, 2016 1 of 7 UbuntuOpenbox.com Copyright © 2016 by Dat H. -
Ubuntu Kung Fu.Pdf
Prepared exclusively for J.S. Ash Beta Book Agile publishing for agile developers The book you’re reading is still under development. As part of our Beta book program, we’re releasing this copy well before we normally would. That way you’ll be able to get this content a couple of months before it’s available in finished form, and we’ll get feedback to make the book even better. The idea is that everyone wins! Be warned. The book has not had a full technical edit, so it will con- tain errors. It has not been copyedited, so it will be full of typos and other weirdness. And there’s been no effort spent doing layout, so you’ll find bad page breaks, over-long lines with little black rectan- gles, incorrect hyphenations, and all the other ugly things that you wouldn’t expect to see in a finished book. We can’t be held liable if you use this book to try to create a spiffy application and you somehow end up with a strangely shaped farm implement instead. Despite all this, we think you’ll enjoy it! Throughout this process you’ll be able to download updated PDFs from your account on http://pragprog.com. When the book is finally ready, you’ll get the final version (and subsequent updates) from the same address. In the meantime, we’d appreciate you sending us your feedback on this book at http://books.pragprog.com/titles/ktuk/errata, or by using the links at the bottom of each page.