A Taxonomy of Attacks Against XML Digital Signatures & Encryption
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-

On the Integrity and Trustworthiness of Web Produced Data
CORE Metadata, citation and similar papers at core.ac.uk Provided by Open Repository of the University of Porto On the Integrity and Trustworthiness of web produced data Luís A. Maia Mestrado Integrado em Engenharia de Redes e Sistemas Informáticos Departamento de Ciência de Computadores 2013 Orientador Professor Doutor Manuel Eduardo Carvalho Duarte Correia, Professor Auxiliar do Departamento de Computadores, Faculdade de Ciências da Universidade do Porto Todas as correções determinadas pelo júri, e só essas, foram efetuadas. O Presidente do Júri, Porto, ______/______/_________ Acknowledgments I would like to express my appreciation for the help of my supervisor in researching and bringing different perspectives and to thank my family, for their support and dedication. 3 Abstract Information Systems have been a key tool for the overall performance improvement of administrative tasks in academic institutions. While most systems intend to deliver a paperless environment to each institution it is recurrent that document integrity and accountability is still relying on traditional methods such as producing physical documents for signing and archiving. While this method delivers a non-efficient work- flow and has an effective monetary cost, it is still the common method to provide a degree of integrity and accountability on the data contained in the databases of the information systems. The evaluation of a document signature is not a straight forward process, it requires the recipient to have a copy of the signers signature for comparison and training beyond the scope of any office employee training, this leads to a serious compromise on the trustability of each document integrity and makes the verification based entirely on the trust of information origin which is not enough to provide non-repudiation to the institutions. -

XML Signature/Encryption — the Basis of Web Services Security
Special Issue on Security for Network Society Falsification Prevention and Protection Technologies and Products XML Signature/Encryption — the Basis of Web Services Security By Koji MIYAUCHI* XML is spreading quickly as a format for electronic documents and messages. As a consequence, ABSTRACT greater importance is being placed on the XML security technology. Against this background research and development efforts into XML security are being energetically pursued. This paper discusses the W3C XML Signature and XML Encryption specifications, which represent the fundamental technology of XML security, as well as other related technologies originally developed by NEC. KEYWORDS XML security, XML signature, XML encryption, Distributed signature, Web services security 1. INTRODUCTION 2. XML SIGNATURE XML is an extendible markup language, the speci- 2.1 Overview fication of which has been established by the W3C XML Signature is an electronic signature technol- (WWW Consortium). It is spreading quickly because ogy that is optimized for XML data. The practical of its flexibility and its platform-independent technol- benefits of this technology include Partial Signature, ogy, which freely allows authors to decide on docu- which allows an electronic signature to be written on ment structures. Various XML-based standard for- specific tags contained in XML data, and Multiple mats have been developed including: ebXML and Signature, which enables multiple electronic signa- RosettaNet, which are standard specifications for e- tures to be written. The use of XML Signature can commerce transactions, TravelXML, which is an EDI solve security problems, including falsification, spoof- (Electronic Data Interchange) standard for travel ing, and repudiation. agencies, and NewsML, which is a standard specifica- tion for new distribution formats. -
Sams Teach Yourself XML in 21 Days
Steven Holzner Teach Yourself XML in 21 Days THIRD EDITION 800 East 96th Street, Indianapolis, Indiana, 46240 USA Sams Teach Yourself XML in 21 Days, ASSOCIATE PUBLISHER Michael Stephens Third Edition ACQUISITIONS EDITOR Copyright © 2004 by Sams Publishing Todd Green All rights reserved. No part of this book shall be reproduced, stored in a retrieval DEVELOPMENT EDITOR system, or transmitted by any means, electronic, mechanical, photocopying, record- Songlin Qiu ing, or otherwise, without written permission from the publisher. No patent liability MANAGING EDITOR is assumed with respect to the use of the information contained herein. Although every precaution has been taken in the preparation of this book, the publisher and Charlotte Clapp author assume no responsibility for errors or omissions. Nor is any liability assumed PROJECT EDITOR for damages resulting from the use of the information contained herein. Matthew Purcell International Standard Book Number: 0-672-32576-4 INDEXER Library of Congress Catalog Card Number: 2003110401 Mandie Frank PROOFREADER Printed in the United States of America Paula Lowell First Printing: October 2003 TECHNICAL EDITOR 06050403 4321 Chris Kenyeres Trademarks TEAM COORDINATOR Cindy Teeters All terms mentioned in this book that are known to be trademarks or service marks have been appropriately capitalized. Sams Publishing cannot attest to the accuracy INTERIOR DESIGNER of this information. Use of a term in this book should not be regarded as affecting Gary Adair the validity of any trademark or service mark. COVER DESIGNER Warning and Disclaimer Gary Adair PAGE LAYOUT Every effort has been made to make this book as complete and as accurate as possi- ble, but no warranty or fitness is implied. -

Bibliography of Erik Wilde
dretbiblio dretbiblio Erik Wilde's Bibliography References [1] AFIPS Fall Joint Computer Conference, San Francisco, California, December 1968. [2] Seventeenth IEEE Conference on Computer Communication Networks, Washington, D.C., 1978. [3] ACM SIGACT-SIGMOD Symposium on Principles of Database Systems, Los Angeles, Cal- ifornia, March 1982. ACM Press. [4] First Conference on Computer-Supported Cooperative Work, 1986. [5] 1987 ACM Conference on Hypertext, Chapel Hill, North Carolina, November 1987. ACM Press. [6] 18th IEEE International Symposium on Fault-Tolerant Computing, Tokyo, Japan, 1988. IEEE Computer Society Press. [7] Conference on Computer-Supported Cooperative Work, Portland, Oregon, 1988. ACM Press. [8] Conference on Office Information Systems, Palo Alto, California, March 1988. [9] 1989 ACM Conference on Hypertext, Pittsburgh, Pennsylvania, November 1989. ACM Press. [10] UNIX | The Legend Evolves. Summer 1990 UKUUG Conference, Buntingford, UK, 1990. UKUUG. [11] Fourth ACM Symposium on User Interface Software and Technology, Hilton Head, South Carolina, November 1991. [12] GLOBECOM'91 Conference, Phoenix, Arizona, 1991. IEEE Computer Society Press. [13] IEEE INFOCOM '91 Conference on Computer Communications, Bal Harbour, Florida, 1991. IEEE Computer Society Press. [14] IEEE International Conference on Communications, Denver, Colorado, June 1991. [15] International Workshop on CSCW, Berlin, Germany, April 1991. [16] Third ACM Conference on Hypertext, San Antonio, Texas, December 1991. ACM Press. [17] 11th Symposium on Reliable Distributed Systems, Houston, Texas, 1992. IEEE Computer Society Press. [18] 3rd Joint European Networking Conference, Innsbruck, Austria, May 1992. [19] Fourth ACM Conference on Hypertext, Milano, Italy, November 1992. ACM Press. [20] GLOBECOM'92 Conference, Orlando, Florida, December 1992. IEEE Computer Society Press. http://github.com/dret/biblio (August 29, 2018) 1 dretbiblio [21] IEEE INFOCOM '92 Conference on Computer Communications, Florence, Italy, 1992. -
Feasibility and Performance Evaluation of Canonical XML
Feasibility and Performance Evaluation of Canonical XML Student Research Project Manuel Binna Student: E-mail: [email protected] Matriculation Number: 108004202162 Supervisor: Dipl.-Inf. Meiko Jensen Period: 20.07.2010 - 19.10.2010 Chair for Network and Data Security Prof. Dr. Jörg Schwenk Faculty of Electrical Engineering and Information Technology Ruhr University Bochum Feasibility and Performance Evaluation of Canonical XML Manuel Binna Abstract Within the boundaries of the XML specification, XML documents can be formatted in various ways without losing the logical equivalence of its content within the scope of the application. However, some applications like XML Signature cannot deal with this flexibility, thus needing a definite textual representation in order to distinguish changes which do or do not alter the logical equivalence of XML content. Canonical XML provides a method to transform textually different yet logically equivalent XML content into a single definite textual representation. This work evaluates the upcoming new major version Canonical XML Version 2.0 with respect to feasibility and performance. Chair for Network and Data Security, Ruhr University Bochum 2 Feasibility and Performance Evaluation of Canonical XML Manuel Binna Declaration I hereby declare that the content of this thesis is a work of my own and that it is original to the best of my knowledge, except where indicated by references to other sources. ____________________________ ______________________________________ Location, Date Signature Chair for Network and Data Security, Ruhr University Bochum 3 Feasibility and Performance Evaluation of Canonical XML Manuel Binna Table of Contents 1. Introduction! 5 1.1.XML 5 1.2.Canonicalization 6 1.3.History 7 1.4.Canonicalization and XML Signature 16 2. -
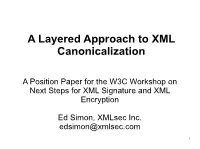
A Layered Approach to XML Canonicalization
A Layered Approach to XML Canonicalization A Position Paper for the W3C Workshop on Next Steps for XML Signature and XML Encryption Ed Simon, XMLsec Inc. [email protected] 1 Background ● XML Canonicalization enables reliable textual and binary comparison of XML documents through the removal of irrelevant differences in structure and content ● Current approach is to write a single specification that details how all parts of XML instances are to be canonicalized ● Proposed alternative approach is to layer canonicalization rules according to the XML stack: core, schema-specific, namespace-specific ● Potential advantages include flexibility and significant optimization of processing 2 Canonicalization Layers ● Core – Normalizes the elements, attributes, and whitespace of an XML instance ● Schema-Aware – Normalization of schema- aware aspects including default attributes, schema-defined data types, etc ● Namespace-Aware – Normalization of XML information set nodes that belong to, or are contained by nodes that belong to, an XML node declared with a particular namespace. Includes the normalization of namespace declarations themselves. 3 Core Canonicalization ● Defined much as per W3C XML Canonicalization version 1.1 ● Only canonicalizes what can be derived from the text of the XML instance ● Includes formatting of XML elements and attributes, whitespace, line breaks, CDATA, entities, etc... ● No namespace normalization (but don't worry, it's coming!) 4 Core Canonicalization Example <xsl:stylesheet version='2.0' xmlns="http://www.w3.org/1999/xhtml" xmlns:xsl="http://www.w3.org/1999/XSL/Transform" xmlns:ns1="http://www.xmlsec.com/namespaces/a" > <xsl:template match="/"> <p>Total Amount: <xsl:value-of ... ...select="ns1:expense-report/ns1:total"/></p> </xsl:template> </xsl:stylesheet> ...will be, after core canonicalization, found to be identical to.. -

Exploring the XML World
Lars Strandén SP Swedish National Testing and Research Institute develops and transfers Exploring the XML World technology for improving competitiveness and quality in industry, and for safety, conservation of resources and good environment in society as a whole. With - A survey for dependable systems Swedens widest and most sophisticated range of equipment and expertise for technical investigation, measurement, testing and certfi cation, we perform research and development in close liaison with universities, institutes of technology and international partners. SP is a EU-notifi ed body and accredited test laboratory. Our headquarters are in Borås, in the west part of Sweden. SP Swedish National Testing and Research Institute SP Swedish National Testing SP Electronics SP REPORT 2004:04 ISBN 91-7848-976-8 ISSN 0284-5172 SP Swedish National Testing and Research Institute Box 857 SE-501 15 BORÅS, SWEDEN Telephone: + 46 33 16 50 00, Telefax: +46 33 13 55 02 SP Electronics E-mail: [email protected], Internet: www.sp.se SP REPORT 2004:04 Lars Strandén Exploring the XML World - A survey for dependable systems 2 Abstract Exploring the XML World - A survey for dependable systems The report gives an overview of and an introduction to the XML world i.e. the definition of XML and how it can be applied. The content shall not be considered a development tutorial since this is better covered by books and information available on the Internet. Instead this report takes a top-down perspective and focuses on the possibilities when using XML e.g. concerning functionality, tools and supporting standards. Getting started with XML is very easy and the threshold is low. -
Information Integration with XML
Information Integration with XML Chaitan Baru Richard Marciano {baru,marciano}@sdsc.edu Data Intensive Computing Environments (DICE) Group San Diego Supercomputer Center National Partnership for Advanced Computational Infrastructure San Diego Supercomputer Center Members of the DICE Group • Staff • Students • Chaitan Baru • Pratik Mukhopadhyay • Amarnath Gupta • Azra Mulic • Bertram Ludäscher • Kevin Munroe • Richard Marciano • Paul Nguyen • Reagan Moore • Michail Petropolis • Yannis Papakonstantinou • Nicholas Puz • Arcot Rajasekar • Pavel Velikhov • Wayne Schroeder • Michael Wan • Ilya Zaslavsky Tutorial Outline • PART I • Introduction to XML • The MIX Project • PART II • Storing/retrieving XML documents • XML and GIS • Open Issues Information Integration with XML PART I • Introduction to XML • HTML vs. XML • XML Industry Initiatives • DTD, Schema, Namespaces • DOM, SAX • XSL, XSLT • Tools • The MIX Project Introduction to XML • SGML (Standard Generalized Markup Language) • ISO Standard, 1986, for data storage & exchange • Used in U.S. gvt. & contractors, large manufacturing companies, technical info. Publishers. • HTML, a simple application of SGML, 1992 - 1999 • SGML reference is 600 pages long • XML (eXtensible Markup Language) • W3C (World Wide Web Consortium) -- http://www.w3.org/XML/) recommendation in 1998 • Simple subset of SGML: “The ASCII of the Web”. • XML specification is 26 pages long • Canonical XML • equivalence testing of XML documents • SML (Simple Markup Language) • No Attributes / No Processing Instructions (PI) / -

Extensible Layout in Functional Documents♦
♦ Extensible layout in functional documents John Lumley, Roger Gimson, Owen Rees Digital Media Systems Laboratory HP Laboratories Bristol HPL-2005-223 December 22, 2005* XML, XSLT, Highly customised variable-data documents make automatic layout of the SVG, document resulting publication hard. Architectures for defining and processing such layout, functional documents can benefit if the repertoire of layout methods available can programming be extended smoothly and easily to accommodate new styles of customisation. The Document Description Framework incorporates a model for declarative document layout and processing where documents are treated as functional programs. A canonical XML tree contains nodes describing layout instructions which will modify and combine their children component parts to build sections of the final presentation. Leaf components such as images, vector graphic fragments and text blocks are 'rendered' to make consistent graphical atoms. These parts are then processed by layout agents, described and parameterised by their parent nodes, which can range from simple layouts like translations, flows, encapsulations and tables through to highly complex arrangements such as constraint-solution or pagination. The result then becomes a 'molecule' for processing at a higher level of the layout tree. A variable and reference mechanism is included for resolving rendering interdependency and supporting component reuse. Addition of new layout types involves definition of a new combinator node and attachment of a suitable agent. * Internal Accession Date Only ♦ IS&T/SPIE Symposium Electronic Imaging, January 2006, San Jose, CA, USA Approved for External Publication © Copyright 2006 Society of Photo-Optical Instrumentation Engineers. This paper is made available as an electronic reprint with permission of SPIE. -
Oracle Xml Db
5 Database Support for XML This chapter contains the following sections: ■ What are the Oracle9i Native XML Database Features? ■ XMLType Datatype ■ When to use XMLType ■ XMLType Storage in the Database ■ XMLType Functions ■ Manipulating XML Data in XMLType Columns ■ Selecting and Querying XML Data ■ Indexing XMLType columns ■ Java Access to XMLType (oracle.xdb.XMLType) ■ DBMS_XMLGEN ■ SYS_XMLGEN ■ SYS_XMLAGG ■ TABLE Functions ■ Frequently Asked Questions (FAQs): XMLType Database Support for XML 5-1 What are the Oracle9i Native XML Database Features? What are the Oracle9i Native XML Database Features? Oracle9i supports XMLType, a new system defined object type. XMLType has built-in member functions that offer a powerful mechanism to create, extract and index XML data. Users can also generate XML documents as XMLType instances dynamically using the SQL functions, SYS_XMLGEN and SYS_XMLAGG, and the PL/SQL package DBMS_XMLGEN. Table 5–1 summarizes the new XML features natively supported in Oracle9i. Table 5–1 Oracle9i Native XML Support Feature Summary XML Feature Description XMLType (new) XMLType is a system defined datatype with predefined member functions to access XML data. You can perform the following tasks with XMLType: ■ Create columns of XMLType and use XMLType member functions on instances of the type. See "XMLType Datatype" on page 5-3. ■ Create PL/SQL functions and procedures, with XMLType as argument and return parameters. See, "When to use XMLType" on page 5-8. ■ Store, index, and manipulate XML data in XMLType columns. Refer to "XMLType Datatype" on page 5-3. DBMS_XMLGEN (new) DBMS_XMLGEN is a PL/SQL package that converts the results of SQL queries to canonical XML format, returning it as XMLType or CLOB. -
XML Technologies Dissected
Spotlight XML Technologies Dissected Erik Wilde • Swiss Federal Institute of Technology, Zürich The lack of well-defined information models in many XML technologies can generate compatibility problems and lower the odds of their long-term success. ML technologies have become ubiquitous izing the entities or an API for accessing the in applications for computer communica- entities from within applications. X tions, business-to-business IT architec- tures, and Web-based services. They are evolving It’s important to clearly distinguish between the rapidly, with developer requirements fueling both properties of an information model and those of its the maturation of core technologies and the emer- data model. For example, I’m concerned here only gence of new ones. However, many of these XML with passive data structures. This might at times technologies lack well-designed support, making seem contradictory. The Document Object Model’s life harder for developers and creating possible application programming interface, for example, obstacles to ultimate success. clearly provides operations for such things as Here, I systematically examine the information adding attributes to elements. However, this is not and data models of several influential XML tech- a feature of the DOM information model of XML, nologies. I define information model and data which simply defines that elements can have any model in keeping with the terms discussed in RFC number of attributes. The DOM API as a data model 3444.1 In doing so, my hope is that the clarification provides functions for inserting attributes, but this that this RFC offers can both benefit XML tech- is essentially the same as using the XML serializa- nologies and help identify areas for future work. -
![[ Team Lib ] .NET & XML Provides an In-Depth, Concentrated Tutorial for Intermediate to Advanced-Level Developers. Additiona](https://docslib.b-cdn.net/cover/4022/team-lib-net-xml-provides-an-in-depth-concentrated-tutorial-for-intermediate-to-advanced-level-developers-additiona-3114022.webp)
[ Team Lib ] .NET & XML Provides an In-Depth, Concentrated Tutorial for Intermediate to Advanced-Level Developers. Additiona
[ Team LiB ] • Table of Contents • Index • Reviews • Reader Reviews • Errata • Academic .NET and XML By Niel M. Bornstein Publisher: O'Reilly Pub Date: November 2003 ISBN: 0-596-00397-8 Pages: 464 .NET & XML provides an in-depth, concentrated tutorial for intermediate to advanced-level developers. Additionally, it includes a complete reference to the XML-related namespaces within the .NET Framework. XML is an extremely flexible technology, and Microsoft has implemented most of the tools programmers need to use it very extensively. .NET & XML aims to help you understand the intersection between the two technologies for maximum effectiveness. [ Team LiB ] [ Team LiB ] • Table of Contents • Index • Reviews • Reader Reviews • Errata • Academic .NET and XML By Niel M. Bornstein Publisher: O'Reilly Pub Date: November 2003 ISBN: 0-596-00397-8 Pages: 464 Copyright Preface Organization of This Book Who Should Read This Book? About XML and Web Services About the Sample Code Why C#? Style Conventions How to Contact Us Acknowledgments Part I: Processing XML with .NET Chapter 1. Introduction to .NET and XML Section 1.1. The .NET Framework Section 1.2. The XML Family of Standards Section 1.3. Introduction to XML in .NET Section 1.4. Key Concepts Section 1.5. Moving On Chapter 2. Reading XML Section 2.1. Reading Data Section 2.2. XmlReader Section 2.3. Moving On Chapter 3. Writing XML Section 3.1. Writing Data Section 3.2. XmlWriter and Its Subclasses Section 3.3. Moving On Chapter 4. Reading and Writing Non-XML Formats Section 4.1. Reading Non-XML Documents with XmlReader Section 4.2.