Plugin-Based Distributed Multi-User Web Applications with Plux
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-

BOROUGH of MANHATTAN COMMUNITY COLLEGE City University of New York Department of Computer Information Systems Office S150/Phone: 212-220-1476
BOROUGH OF MANHATTAN COMMUNITY COLLEGE City University of New York Department of Computer Information Systems Office S150/Phone: 212-220-1476 Web Programming II Class hours: 2 CIS 485 Lab hours: 2 Spring 2012 Credits: 3 Course Description: This course will introduce students to server-side web programming. Emphasis is placed on database connectivity in order to solve intermediate level application problems. Students will be tasked with web projects that facilitate understanding of tier design and programming concepts. The overall goal of this course is to create a shopping cart application with a login and database component. Prerequisites/Co-requisite: Basic Skills: ENG 088, ESL 062, ACR 094, MAT 012/051; CIS 385 Web Programming I Learning Outcomes and Assessment After completing this course, students will be able to: Outcome: Demonstrate the use of a database with server-side scripting Assessment: Lab exercises and exam questions Outcome: Demonstrate the use a Cookie and Session manager with server-side scripting Assessment: Final project, lab exercises and exam questions Outcome: Develop a database-driven website Assessment: Lab exercises Outcome: Design and develop a shopping-cart application with a login and database component Assessment: Final Project General Education Outcomes and Assessment Quantitative Skills – Students will use quantitative skills and concepts and methods of mathematics to solve problems Assessment: Use formulas and concepts of mathematics to solve problems in programming assignments Information and Technology -

DLCGI Advanced Uses
DLCGI Advanced Uses Using DLCGI to achieve single sign-on with The Diver Solution In situations where authentication to DiveLine needs to be integrated with an existing authentication scheme, we provide "DLCGI", the DiveLine-Common Gateway Interface interfacing module. The "Common Gateway Interface" is a standard for interfacing external scripts and programs with a web server. How DLCGI works When dlcgi.exe is executed by the webserver, in the context of a user that the web server has already authenticated, it obtains a limited-lifetime one-time password from DiveLine. This password can be passed, via web page redirects, custom web page scripting, etc., to DivePort, NetDiver, or even ProDiver to allow the user to login. The typical strategy for using DLCGI is: 1. Configure DiveLine to accept DLCGI requests from your webserver. 2. Install dlcgi.exe in a scripts directory (e.g. /cgi-bin/) on your CGI-compliant webserver (e.g. IIS, Apache). You configure the name of your DiveLine server and other parameters using dlcgi.cfg in the same directory as the executable. 3. Restrict access to this script so that the webserver will only execute it when the user has already authenticated (e.g. Domain account). Typical uses • DivePort: Users go to the DivePort site, and are redirected to another URL for authentication. That URL, which runs dlcgi.exe, redirects the user back to the DivePort URL with a one-use authentication token. • ProDiver: When ProDiver connects to DiveLine, if configured with a DLCGI URL, it will access the URL in "raw" mode (see below) to obtain a parse-able result file containing a one-use DiveLine authentication token. -

Leukemia Medical Application with Security Features
Journal of Software Leukemia Medical Application with Security Features Radhi Rafiee Afandi1, Waidah Ismail1*, Azlan Husin2, Rosline Hassan3 1 Faculty Science and Technology, Universiti Sains Islam Malaysia, Negeri Sembilan, Malaysia. 2 Department of Internal Medicine, School of Medicine, Universiti Sains Malaysia, Kota Bahru, Malaysia. 3 Department of Hematology, School of Medicine, Universiti Sains Malaysia, Kota Bahru, Malaysia. * Corresponding author. Tel.: +6 06 7988056; email: [email protected]. Manuscript submitted January 27, 2015; accepted April 28, 2015 doi: 10.17706/jsw.10.5.577-598 Abstract: Information on the Leukemia patients is very crucial by keep track medical history and to know the current status of the patient’s. This paper explains on development of Hematology Information System (HIS) in Hospital Universiti Sains Malaysia (HUSM). HIS is the web application, which is the enhancement of the standalone application system that used previously. The previous system lack of the implementation of security framework and triple ‘A’ elements which are authentication, authorization and accounting. Therefore, the objective of this project is to ensure the security features are implemented and the information safely kept in the server. We are using agile methodology to develop the HIS which the involvement from the user at the beginning until end of the project. The user involvement at the beginning user requirement until implemented. As stated above, HIS is web application that used JSP technology. It can only be access within the HUSM only by using the local Internet Protocol (IP). HIS ease medical doctor and nurse to manage the Leukemia patients. For the security purpose HIS provided password to login, three different user access levels and activity log that recorded from each user that entered the system Key words: Hematology information system, security feature, agile methodology. -

Getting Started Guide with Wiz550web Getting Started Guide with Wiz550web
2015/02/09 17:48 1/21 Getting Started Guide with WIZ550web Getting Started Guide with WIZ550web WIZ550web is an embedded Web server module based on WIZnet’s W5500 hardwired TCP/IP chip, Users can control & monitor the 16-configurable digital I/O and 4-ADC inputs on module via web pages. WIZ550web provides the firmware & web page examples for user’s customization. This page describes the following topics: ● Product Preview ● Hello world ❍ Product contents ❍ SD card initialization ❍ Data flash initialization ❍ Serial debug message ● WIZ550web Basic operations and CGI ● Basic Demo Webpage ● Examples for WIZ550web customization Users can download the following source codes from the 'WIZ550web GitHub Repository' ● Firmware source code (The projects for Eclipse IDE) ❍ Application / Boot ● Demo webpage WIZ550web GitHub Repository https://github.com/Wiznet/WIZ550web WIZ550web GitHub Page http://wiznet.github.io/WIZ550web Develop Environment - http://wizwiki.net/wiki/ Last update: 2015/02/09 products:wiz550web:wiz550webgsg_en http://wizwiki.net/wiki/doku.php?id=products:wiz550web:wiz550webgsg_en 13:05 ● Eclipse IDE for C/C++ Developers, Kepler Service Release 2 ● ARM GCC 4.8.3 (2014q1) Product Preview Hello World Product Contents Ordering Part No: WIZ550web ● WIZ550web module x 1 Ordering Part No: WIZ550web-EVB ● WIZ550web module x 1 ● WIZ550web baseboard x 1 http://wizwiki.net/wiki/ Printed on 2015/02/09 17:48 2015/02/09 17:48 3/21 Getting Started Guide with WIZ550web ● LAN cable x 1 ● Serial cable x 1 ● 12V Power adapter x 1 SD card is option for both WIZ550web and WIZ550web-EVB Refer to recommended lists of SD card. Vendor Capacity(Bytes) Type Class 2G SD n/a Sandisk 4G SDHC 4 8G SDHC 4 Samsung 4G SDHC 6 Transcend 4G SDHC 4,10 SD card Initialization WIZ550web uses Micro SD card as a storage for web content and SD card is not included as default. -

CGI Scripts: Gateways to World-Wide Web Power
Behavior Research Methods. Instruments. & Computers 1996,28 (2), 165-169 CGI scripts: Gateways to World-Wide Web power JAMES M. KIELEY Miyazaki International CoUege, Miyazaki, Japan The power of the hypertext-based information presentation system known as the World-Wide Web can be enhanced by scripts based on the common gateway interface (CG!) protocol. CG! scripts re siding on a Webserver permit the execution of computer programs that can perform a wide variety of functions that maybe useful to psychologists. Example applications are presented here, along with ref erence information for potential script developers. The majority ofinformation that people access via the permit users to input data by clicking on checkboxes, hypertext-based information presentation system known radio buttons, menus, reset buttons, and submit buttons, as the World-Wide Web (WWW) is actually stored in the and also by typing into text fields (Lemay, 1995). form of static files-that is, text and graphics files that COl was developed by the original programmers ofthe appear a certain way when viewed from a Web browser, UNIX-based CERN and NCSA HTTP Web servers to such as Netscape or Mosaic, because ofa command lan supersede a prior scripting environment called HTBIN. guage known as HTML. HTML, by its original design, is Other Web servers that support scripting, including those a simple command set used to present multimedia infor based on other operating systems, mayor may not use mation that can be accessed asynchronously. The capa the COl protocol. Early applications of COl scripts in bilities ofHTML, and, therefore, the WWW, can be im cluded using them to serve information to a browser that proved with scripts conforming to the common gateway is in a format that is otherwise unreadable, such as an SQL interface (COl) protocol. -
The Common Gateway Interface and Server-Side Programming
WebWeb MasterMaster 11 IFIIFI Andrea G. B. Tettamanzi Université de Nice Sophia Antipolis Département Informatique [email protected] Andrea G. B. Tettamanzi, 2019 1 Unit 3 The Common Gateway Interface and Server-side Programming Andrea G. B. Tettamanzi, 2019 2 Agenda • The Common Gateway Interface • Server-Side Programming Andrea G. B. Tettamanzi, 2019 3 Introduction • An HTTP server is often used as a gateway to a different information system (legacy or not), for example – an existing body of documents – an existing database application • The Common Gateway Interface (CGI) is an agreement between HTTP server implementors about how to integrate such gateway scripts and programs • It was typically (but not exclusively) used in conjunction with HTML forms to build database applications • Nowadays largely superseded by dynamic Web content technologies such as PHP, ASP.NET, Java Servlets, and Node.js Andrea G. B. Tettamanzi, 2019 4 The Common Gateway Interface • The Common Gateway Interface (CGI) is a de facto standard protocol for Web servers to execute an external program that generates a Web page dynamically • The external program executes like a console application running on the same machine as the Web server (the host) • Such program is known as a CGI script or simply as a CGI Andrea G. B. Tettamanzi, 2019 5 How Does That Work? • Each time a client requests the URL corresponding to a CGI program, the server will execute it in real-time – E.g.: GET http://www.example.org/cgi-bin/add?x=2&y=2 • The output of the program will go more or less directly to the client • Strictly speaking, the “input” to the program is the HTTP request • Environment variables are used to pass data about the request from the server to the program – They are accessed by the script in a system-defined manner – Missing environment variable = NULL value – Character encoding is system-defined Andrea G. -
Common Gateway Interface Reference Guide
COMMON GATEWAY INTERFACE REFERENCE GUIDE Copyright © 1998 The President and Fellows of Harvard College All rights reserved Common Gateway Interface (CGI) Reference Guide The Harvard Computer Society Table of Contents Introduction...............................................................................................................................................................1 How the Web Really Works ...................................................................................................................................1 GET and POST ......................................................................................................................................................1 Perl and CGI ..............................................................................................................................................................2 Here Document Quoting ........................................................................................................................................2 The CGI.pm Module...............................................................................................................................................2 Returning a Web Page...........................................................................................................................................3 Sending Mail ..........................................................................................................................................................4 Maintaining State......................................................................................................................................................5 -
Dynamic Web Content Technologies
Dynamic web content technologies CSCI 470: Web Science • Keith Vertanen Overview • Dynamic content – What it is – Sources of input • CGI (Common Gateway Interface) – FastCGI • Server-side scripng – PHP, ASP, JSP • Web server modules • Custom web server 2 Stac vs. dynamic • Stac content – Images and pages don't change • Always the same, liKe a file server – Fast to deliver, easy to cache • Dynamic content – Same URL results in different delivered HTML • e.g. different preference on # of products to display – May change as user interac?on progresses • e.g. adding items to a shopping cart – Need something besides just HTTP and HTML • HTTP is stateless • HTML is not programmable (e.g. condi?onal, loops) 3 Input to dynamic pages • Form fields – <INPUT> tags inside the <FORM> tag – URL encoding (percent-encoded) • if GET: in the URL, if POST: in the HTTP payload • Unreserved characters: – ABCDEFGHIJKLMNOPQRSTUVWXYZ abcdefghijKlmnopqrstuvwxyz0123456789-_.~ • Reserved characters: – !*'();:@&=$,/?#[] – Converted to %XX, where XX is ASCII in hexadecimal – %20 = space (also +), %21 = !, %23 = #, %25 = %, … • Most languages have URL encode/decode func?ons 4 Input to dynamic pages • Cookies – Differen?ate clients hing same page • Other input sources: – User agent (browser) – HTTP referer • Misspelled since original RFC 1945 • The page you came from to get to this one – Client's IP address – Time of day – … 5 CGI • CGI (Common Gateway Interface) – In use since 1993 – Requests a URL in a special locaon/file extension • e.g. h~p://www.blah.com/cgi-bin/looKup -

Lecture Forms and Common Gateway Interface Mechanism
Lecture Forms and Common Gateway Interface Mechanism 6WXaZ(OP\,c,.TT(0,1$'W_(+b,)111%78786:# 4 Forms • Used to create a set of pages that contain fields in which the viewer can select and supply information – Introduced very early in HTML 2.0 – Allows WWW users to perform data entry – Permit direct interaction with customers for inquiries, registration, sales of products, and services – To create a capability requires two steps: • Use HTML form elements to create the pages that contain the form • Write a server-side script to process form data; this program must be placed so the WWW server can execute it 6WXaZ(OP\,c,.TT(0,1$'W_(+b,)111%78786:# 7 The Original Set of User Interface Elements %-0154' 4/01 A9B/ (DCHE/ .2/348CI 2789C:5;11CB ,G8A91 68'0.7 2/E/1 5(6(7 17EEHCD: )))) %4(64'2('' *0/ %,(.(.4' $(), $:007 $5=0 6WXaZ(OP\,c,.TT(0,1$'W_(+b,)111%78786:# 9 FORM Element and Some Attributes • Syntax <FORM> ... </FORM> • Attribute Specifications – ACTION= URI (form handler) – METHOD=[ get | post ] (HTTP method for submitting form) • GET is the default; form contents are appended to the URL • POST form contents to be sent as payload – ENCTYPE= ContentType (content type to submit form as) • Defaults to application/x-www-urlencoded which returns name/value pairs, separated by &, spaces replaced by + and reserved characters (like #) replaced by %HH, H a hex digit – ACCEPT-CHARSET= Charsets (supported character encodings) – TARGET= FrameTarget (frame to render form result in, in HTML4) (a browsing context name or keyword, in HTML5, such as _self, -
Server Side Programming
SAN DIEGO COMMUNITY COLLEGE DISTRICT CONTINUING EDUCATION COURSE OUTLINE SECTION I SUBJECT AREA AND COURSE NUMBER COMP 623 COURSE TITLE SERVER SIDE PROGRAMMING TYPE COURSE NON-FEE VOCATIONAL CATALOG COURSE DESCRIPTION In this course students will learn how to deliver dynamic content on Web sites. This course covers Server Side programming, (such as ASP.NET, CGI, Java VM, MySQL, and Fast CGI). Students will also learn about extending Web server software through configuring and scripting. (FT) LECTURE/LABORATORY HOURS 250 ADVISORY NONE RECOMMENDED SKILL LEVEL Possess a 10th grade reading level; ability to communicate effectively in the English language; knowledge of math concepts at the 8th grade level; ability to use a mouse, menus, open and close windows and save files within the Macintosh or Windows operating system; and ability to use an internet browser. INSTITUTIONAL STUDENT LEARNING OUTCOMES 1. Social Responsibility SDCE students demonstrate interpersonal skills by learning and working cooperatively in a diverse environment. 2. Effective Communication SDCE students demonstrate effective communication skills. CEISO 02/07; Revised 12/18/13 SERVER SIDE PROGRAMMING PAGE 2 INSTITUTIONAL STUDENT LEARNING OUTCOMES (CONTINUED) 3. Critical Thinking SDCE students critically process information, make decisions, and solve problems independently or cooperatively. 4. Personal and Professional Development SDCE students pursue short term and life-long learning goals, mastering necessary skills and using resource management and self advocacy skills to cope with changing situations in their lives. COURSE GOALS To provide instruction in how dynamic content is delivered on the Web. Students will learn about Server-Side includes, the Common Gateway Interface (CGI), and about writing and debugging CGI scripts. -
Maxbox CGI and Websocket
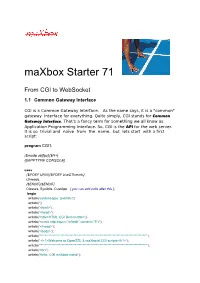
maXbox Starter 71 From CGI to WebSocket 1.1 Common Gateway Interface CGI is a Common Gateway Interface. As the name says, it is a "common" gateway interface for everything. Quite simply, CGI stands for Common Gateway Interface. That’s a fancy term for something we all know as Application Programming Interface. So, CGI is the API for the web server. It is so trivial and naïve from the name, but lets start with a first script: program CGI1; {$mode objfpc}{$H+} {$APPTYPE CONSOLE} uses {$IFDEF UNIX}{$IFDEF UseCThreads} cthreads, {$ENDIF}{$ENDIF} Classes, SysUtils, CustApp { you can add units after this }; begin writeln('content-type: text/html'); writeln(''); writeln('<html>'); writeln('<head>'); writeln('<title>HTML CGI Demo</title>'); writeln('<meta http-equiv="refresh" content="5">'); writeln('</head>'); writeln('<body>'); writeln('**********************************************************************************'); writeln(' <h1>Welcome to OpenSSL & maXbox4 CGI scripts</h1>'); writeln('**********************************************************************************'); writeln('<br>'); writeln('Hello, CGI maXbox world!'); writeln('<br>'); writeln(dateTimetoStr(now)); writeln('</body>'); writeln('</html>') end. //end. The interesting one in above script is the calling of a compiled function writeln(dateTimetoStr(now)); which is an internal function of your language, so you don't need Java Script! Remember also: The server and the client (the browser) usually run on different computers. They may run under different operating systems, even -

Web Programming
Web Programming © Leonidas Fegaras University of Texas at Arlington Web Data Management and XML L2: Web Programming 1 Dynamic Web Pages Static web page: every time you request this page, you get exactly the same content boring! Dynamic web page: the page content may change on each request the user interacts with the web site and the web site responds accordingly Common Gateway Interface (CGI) A simple protocol that can be used to communicate between Web forms and your program A CGI script can be written in any language Need to be able to read input, write to output, and read environment variables PHP, Java, C, C#, Perl, etc Web Data Management and XML L2: Web Programming 2 Web Programming We need both client-side and server-side programming to improve client-server interaction to reduce bandwidth, server load, response time, etc Client-side programming is needed to put dynamic content into an HTML page to react to user events interactively without bothering the server to mimic a GUI using graphics and animation to validate data/queries before they are submitted to the server Server-side programming is needed to limit the client interface to a server for security and performance to perform heavy-duty processing, not available at every client database processing file directory service as a broker to web services Web Data Management and XML L2: Web Programming 3 Current Situation For client-side programming, the choice is clear: JavaScript Java applets were a promising idea but failed For server-side, there are many choices: For rapid prototyping,