Loosely-Self-Stabilizing Byzantine-Tolerant Binary Consensus for Signature-Free Message-Passing Systems
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-

Butler Lampson, Martin Abadi, Michael Burrows, Edward Wobber
Outline • Chapter 19: Security (cont) • A Method for Obtaining Digital Signatures and Public-Key Cryptosystems Ronald L. Rivest, Adi Shamir, and Leonard M. Adleman. Communications of the ACM 21,2 (Feb. 1978) – RSA Algorithm – First practical public key crypto system • Authentication in Distributed Systems: Theory and Practice, Butler Lampson, Martin Abadi, Michael Burrows, Edward Wobber – Butler Lampson (MSR) - He was one of the designers of the SDS 940 time-sharing system, the Alto personal distributed computing system, the Xerox 9700 laser printer, two-phase commit protocols, the Autonet LAN, and several programming languages – Martin Abadi (Bell Labs) – Michael Burrows, Edward Wobber (DEC/Compaq/HP SRC) Oct-21-03 CSE 542: Operating Systems 1 Encryption • Properties of good encryption technique: – Relatively simple for authorized users to encrypt and decrypt data. – Encryption scheme depends not on the secrecy of the algorithm but on a parameter of the algorithm called the encryption key. – Extremely difficult for an intruder to determine the encryption key. Oct-21-03 CSE 542: Operating Systems 2 Strength • Strength of crypto system depends on the strengths of the keys • Computers get faster – keys have to become harder to keep up • If it takes more effort to break a code than is worth, it is okay – Transferring money from my bank to my credit card and Citibank transferring billions of dollars with another bank should not have the same key strength Oct-21-03 CSE 542: Operating Systems 3 Encryption methods • Symmetric cryptography – Sender and receiver know the secret key (apriori ) • Fast encryption, but key exchange should happen outside the system • Asymmetric cryptography – Each person maintains two keys, public and private • M ≡ PrivateKey(PublicKey(M)) • M ≡ PublicKey (PrivateKey(M)) – Public part is available to anyone, private part is only known to the sender – E.g. -

ACM SIGACT News Distributed Computing Column 28
ACM SIGACT News Distributed Computing Column 28 Idit Keidar Dept. of Electrical Engineering, Technion Haifa, 32000, Israel [email protected] Sergio Rajsbaum, who edited this column for seven years and established it as a relevant and popular venue, is stepping down. This issue is my first step in the big shoes he vacated. I would like to take this opportunity to thank Sergio for providing us with seven years’ worth of interesting columns. In producing these columns, Sergio has enjoyed the support of the community at-large and obtained material from many authors, who greatly contributed to the column’s success. I hope to enjoy a similar level of support; I warmly welcome your feedback and suggestions for material to include in this column! The main two conferences in the area of principles of distributed computing, PODC and DISC, took place this summer. This issue is centered around these conferences, and more broadly, distributed computing research as reflected therein, ranging from reviews of this year’s instantiations, through influential papers in past instantiations, to examining PODC’s place within the realm of computer science. I begin with a short review of PODC’07, and highlight some “hot” trends that have taken root in PODC, as reflected in this year’s program. Some of the forthcoming columns will be dedicated to these up-and- coming research topics. This is followed by a review of this year’s DISC, by Edward (Eddie) Bortnikov. For some perspective on long-running trends in the field, I next include the announcement of this year’s Edsger W. -

Edsger Dijkstra: the Man Who Carried Computer Science on His Shoulders
INFERENCE / Vol. 5, No. 3 Edsger Dijkstra The Man Who Carried Computer Science on His Shoulders Krzysztof Apt s it turned out, the train I had taken from dsger dijkstra was born in Rotterdam in 1930. Nijmegen to Eindhoven arrived late. To make He described his father, at one time the president matters worse, I was then unable to find the right of the Dutch Chemical Society, as “an excellent Aoffice in the university building. When I eventually arrived Echemist,” and his mother as “a brilliant mathematician for my appointment, I was more than half an hour behind who had no job.”1 In 1948, Dijkstra achieved remarkable schedule. The professor completely ignored my profuse results when he completed secondary school at the famous apologies and proceeded to take a full hour for the meet- Erasmiaans Gymnasium in Rotterdam. His school diploma ing. It was the first time I met Edsger Wybe Dijkstra. shows that he earned the highest possible grade in no less At the time of our meeting in 1975, Dijkstra was 45 than six out of thirteen subjects. He then enrolled at the years old. The most prestigious award in computer sci- University of Leiden to study physics. ence, the ACM Turing Award, had been conferred on In September 1951, Dijkstra’s father suggested he attend him three years earlier. Almost twenty years his junior, I a three-week course on programming in Cambridge. It knew very little about the field—I had only learned what turned out to be an idea with far-reaching consequences. a flowchart was a couple of weeks earlier. -
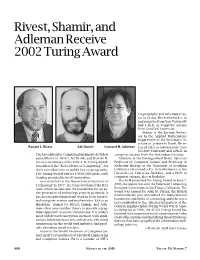
Rivest, Shamir, and Adleman Receive 2002 Turing Award, Volume 50
Rivest, Shamir, and Adleman Receive 2002 Turing Award Cryptography and Information Se- curity Group. He received a B.A. in mathematics from Yale University and a Ph.D. in computer science from Stanford University. Shamir is the Borman Profes- sor in the Applied Mathematics Department of the Weizmann In- stitute of Science in Israel. He re- Ronald L. Rivest Adi Shamir Leonard M. Adleman ceived a B.S. in mathematics from Tel Aviv University and a Ph.D. in The Association for Computing Machinery (ACM) has computer science from the Weizmann Institute. named RONALD L. RIVEST, ADI SHAMIR, and LEONARD M. Adleman is the Distinguished Henry Salvatori ADLEMAN as winners of the 2002 A. M. Turing Award, Professor of Computer Science and Professor of considered the “Nobel Prize of Computing”, for Molecular Biology at the University of Southern their contributions to public key cryptography. California. He earned a B.S. in mathematics at the The Turing Award carries a $100,000 prize, with University of California, Berkeley, and a Ph.D. in funding provided by Intel Corporation. computer science, also at Berkeley. As researchers at the Massachusetts Institute of The ACM presented the Turing Award on June 7, Technology in 1977, the team developed the RSA 2003, in conjunction with the Federated Computing code, which has become the foundation for an en- Research Conference in San Diego, California. The tire generation of technology security products. It award was named for Alan M. Turing, the British mathematician who articulated the mathematical has also inspired important work in both theoret- foundation and limits of computing and who was a ical computer science and mathematics. -

On-The-Fly Garbage Collection: an Exercise in Cooperation
8. HoIn, B.K.P. Determining lightness from an image. Comptr. Graphics and Image Processing 3, 4(Dec. 1974), 277-299. 9. Huffman, D.A. Impossible objects as nonsense sentences. In Machine Intelligence 6, B. Meltzer and D. Michie, Eds., Edinburgh U. Press, Edinburgh, 1971, pp. 295-323. 10. Mackworth, A.K. Consistency in networks of relations. Artif. Intell. 8, 1(1977), 99-118. I1. Marr, D. Simple memory: A theory for archicortex. Philos. Trans. Operating R.S. Gaines Roy. Soc. B. 252 (1971), 23-81. Systems Editor 12. Marr, D., and Poggio, T. Cooperative computation of stereo disparity. A.I. Memo 364, A.I. Lab., M.I.T., Cambridge, Mass., 1976. On-the-Fly Garbage 13. Minsky, M., and Papert, S. Perceptrons. M.I.T. Press, Cambridge, Mass., 1968. Collection: An Exercise in 14. Montanari, U. Networks of constraints: Fundamental properties and applications to picture processing. Inform. Sci. 7, 2(April 1974), Cooperation 95-132. 15. Rosenfeld, A., Hummel, R., and Zucker, S.W. Scene labelling by relaxation operations. IEEE Trans. Systems, Man, and Cybernetics Edsger W. Dijkstra SMC-6, 6(June 1976), 420-433. Burroughs Corporation 16. Sussman, G.J., and McDermott, D.V. From PLANNER to CONNIVER--a genetic approach. Proc. AFIPS 1972 FJCC, Vol. 41, AFIPS Press, Montvale, N.J., pp. 1171-1179. Leslie Lamport 17. Sussman, G.J., and Stallman, R.M. Forward reasoning and SRI International dependency-directed backtracking in a system for computer-aided circuit analysis. A.I. Memo 380, A.I. Lab., M.I.T., Cambridge, Mass., 1976. A.J. Martin, C.S. -

Resource Bounds for Self-Stabilizing Message Driven Protocols
RESOURCE BOUNDS FOR SELF-STABILIZING MESSAGE DRIVEN PROTOCOLS SHLOMI DOLEV¤, AMOS ISRAELIy , AND SHLOMO MORANz Abstract. Self-stabilizing message driven protocols are defined and discussed. The class weak- exclusion that contains many natural tasks such as `-exclusion and token-passing is defined, and it is shown that in any execution of any self-stabilizing protocol for a task in this class, the configuration size must grow at least in a logarithmic rate. This last lower bound is valid even if the system is supported by a time-out mechanism that prevents communication deadlocks. Then we present three self-stabilizing message driven protocols for token-passing. The rate of growth of configuration size for all three protocols matches the aforementioned lower bound. Our protocols are presented for two processor systems but can be easily adapted to rings of arbitrary size. Our results have an interesting interpretation in terms of automata theory. Key words. self-stabilization, message passing, token-passing, shared-memory AMS subject classifications. 68M10, 68M15, 68Q10, 68Q20 1. Introduction. A distributed system is a set of state machines, called pro- cessors, which communicate either by shared variables or by message-passing. In the first case, the system is a shared memory system, in the second case the system is a message-passing system. A distributed system is self-stabilizing if it can be started in any possible global state. Once started, the system regains its consistency by itself, without any kind of an outside intervention. The self-stabilization property is very useful for systems in which processors may crash and then recover spontaneously in an arbitrary state. -

Optical PUF for Non-Forwardable Vehicle Authentication
Computer Communications 93 (2016) 52–67 Contents lists available at ScienceDirect Computer Communications journal homepage: www.elsevier.com/locate/comcom R Optical PUF for Non-Forwardable Vehicle Authentication ∗ Shlomi Dolev a,1, Łukasz Krzywiecki b,2, Nisha Panwar a, , Michael Segal c a Department of Computer Science, Ben-Gurion University of the Negev, Israel b Department of Computer Science, Wrocław University of Technology, Poland c Department of Communication Systems Engineering, Ben-Gurion University of the Negev, Israel a r t i c l e i n f o a b s t r a c t Article history: Modern vehicles are configured to exchange warning messages through IEEE 1609 Dedicated Short Range Available online 1 June 2016 Communication over IEEE 802.11p Wireless Access in Vehicular Environment. Essentially, these warning messages must associate an authentication factor such that the verifier authenticates the message origin Keywords: Authentication via visual binding. Interestingly, the existing vehicle communication incorporates the message forward- Certificate ability as a requested feature for numerous applications. On the contrary, a secure vehicular communica- Wireless radio channel tion relies on a message authentication with respect to the sender identity. Currently, the vehicle security Optical channel infrastructure is vulnerable to message forwarding in a way that allows an incorrect visual binding with Challenge response pairs the malicious vehicle, i.e., messages seem to originate from a malicious vehicle due to non-detectable Verification message relaying instead of the actual message sender. We introduce the non-forwardable authentication to avoid an adversary coalition attack scenario. These messages should be identifiable with respect to the immediate sender at every hop. -
![Arxiv:1909.05204V3 [Cs.DC] 6 Feb 2020](https://docslib.b-cdn.net/cover/9182/arxiv-1909-05204v3-cs-dc-6-feb-2020-359182.webp)
Arxiv:1909.05204V3 [Cs.DC] 6 Feb 2020
Cogsworth: Byzantine View Synchronization Oded Naor, Technion and Calibra Mathieu Baudet, Calibra Dahlia Malkhi, Calibra Alexander Spiegelman, VMware Research Most methods for Byzantine fault tolerance (BFT) in the partial synchrony setting divide the local state of the nodes into views, and the transition from one view to the next dictates a leader change. In order to provide liveness, all honest nodes need to stay in the same view for a sufficiently long time. This requires view synchronization, a requisite of BFT that we extract and formally define here. Existing approaches for Byzantine view synchronization incur quadratic communication (in n, the number of parties). A cascade of O(n) view changes may thus result in O(n3) communication complexity. This paper presents a new Byzantine view synchronization algorithm named Cogsworth, that has optimistically linear communication complexity and constant latency. Faced with benign failures, Cogsworth has expected linear communication and constant latency. The result here serves as an important step towards reaching solutions that have overall quadratic communication, the known lower bound on Byzantine fault tolerant consensus. Cogsworth is particularly useful for a family of BFT protocols that already exhibit linear communication under various circumstances, but suffer quadratic overhead due to view synchro- nization. 1. INTRODUCTION Logical synchronization is a requisite for progress to be made in asynchronous state machine repli- cation (SMR). Previous Byzantine fault tolerant (BFT) synchronization mechanisms incur quadratic message complexities, frequently dominating over the linear cost of the consensus cores of BFT so- lutions. In this work, we define the view synchronization problem and provide the first solution in the Byzantine setting, whose latency is bounded and communication cost is linear, under a broad set of scenarios. -

Resource-Competitive Algorithms1 1 Introduction
Resource-Competitive Algorithms1 Michael A. Bender Varsha Dani Department of Computer Science Department of Computer Science Stony Brook University University of New Mexico Stony Brook, NY, USA Albuquerque, NM, USA [email protected] [email protected] Jeremy T. Fineman Seth Gilbert Department of Computer Science Department of Computer Science Georgetown University National University of Singapore Washington, DC, USA Singapore [email protected] [email protected] Mahnush Movahedi Seth Pettie Department of Computer Science Electrical Eng. and Computer Science Dept. University of New Mexico University of Michigan Albuquerque, NM, USA Ann Arbor, MI, USA [email protected] [email protected] Jared Saia Maxwell Young Department of Computer Science Computer Science and Engineering Dept. University of New Mexico Mississippi State University Albuquerque, NM, USA Starkville, MS, USA [email protected] [email protected] Abstract The point of adversarial analysis is to model the worst-case performance of an algorithm. Un- fortunately, this analysis may not always reflect performance in practice because the adversarial assumption can be overly pessimistic. In such cases, several techniques have been developed to provide a more refined understanding of how an algorithm performs e.g., competitive analysis, parameterized analysis, and the theory of approximation algorithms. Here, we describe an analogous technique called resource competitiveness, tailored for dis- tributed systems. Often there is an operational cost for adversarial behavior arising from band- width usage, computational power, energy limitations, etc. Modeling this cost provides some notion of how much disruption the adversary can inflict on the system. In parameterizing by this cost, we can design an algorithm with the following guarantee: if the adversary pays T , then the additional cost of the algorithm is some function of T . -

Cryptography: DH And
1 ì Key Exchange Secure Software Systems Fall 2018 2 Challenge – Exchanging Keys & & − 1 6(6 − 1) !"#ℎ%&'() = = = 15 & 2 2 The more parties in communication, ! $ the more keys that need to be securely exchanged Do we have to use out-of-band " # methods? (e.g., phone?) % Secure Software Systems Fall 2018 3 Key Exchange ì Insecure communica-ons ì Alice and Bob agree on a channel shared secret (“key”) that ì Eve can see everything! Eve doesn’t know ì Despite Eve seeing everything! ! " (alice) (bob) # (eve) Secure Software Systems Fall 2018 Whitfield Diffie and Martin Hellman, 4 “New directions in cryptography,” in IEEE Transactions on Information Theory, vol. 22, no. 6, Nov 1976. Proposed public key cryptography. Diffie-Hellman key exchange. Secure Software Systems Fall 2018 5 Diffie-Hellman Color Analogy (1) It’s easy to mix two colors: + = (2) Mixing two or more colors in a different order results in + + = the same color: + + = (3) Mixing colors is one-way (Impossible to determine which colors went in to produce final result) https://www.crypto101.io/ Secure Software Systems Fall 2018 6 Diffie-Hellman Color Analogy ! # " (alice) (eve) (bob) + + $ $ = = Mix Mix (1) Start with public color ▇ – share across network (2) Alice picks secret color ▇ and mixes it to get ▇ (3) Bob picks secret color ▇ and mixes it to get ▇ Secure Software Systems Fall 2018 7 Diffie-Hellman Color Analogy ! # " (alice) (eve) (bob) $ $ Mix Mix = = Eve can’t calculate ▇ !! (secret keys were never shared) (4) Alice and Bob exchange their mixed colors (▇,▇) (5) Eve will -

Mathematical Writing by Donald E. Knuth, Tracy Larrabee, and Paul M
Mathematical Writing by Donald E. Knuth, Tracy Larrabee, and Paul M. Roberts This report is based on a course of the same name given at Stanford University during autumn quarter, 1987. Here's the catalog description: CS 209. Mathematical Writing|Issues of technical writing and the ef- fective presentation of mathematics and computer science. Preparation of theses, papers, books, and \literate" computer programs. A term paper on a topic of your choice; this paper may be used for credit in another course. The first three lectures were a \minicourse" that summarized the basics. About two hundred people attended those three sessions, which were devoted primarily to a discussion of the points in x1 of this report. An exercise (x2) and a suggested solution (x3) were also part of the minicourse. The remaining 28 lectures covered these and other issues in depth. We saw many examples of \before" and \after" from manuscripts in progress. We learned how to avoid excessive subscripts and superscripts. We discussed the documentation of algorithms, com- puter programs, and user manuals. We considered the process of refereeing and editing. We studied how to make effective diagrams and tables, and how to find appropriate quota- tions to spice up a text. Some of the material duplicated some of what would be discussed in writing classes offered by the English department, but the vast majority of the lectures were devoted to issues that are specific to mathematics and/or computer science. Guest lectures by Herb Wilf (University of Pennsylvania), Jeff Ullman (Stanford), Leslie Lamport (Digital Equipment Corporation), Nils Nilsson (Stanford), Mary-Claire van Leunen (Digital Equipment Corporation), Rosalie Stemer (San Francisco Chronicle), and Paul Halmos (University of Santa Clara), were a special highlight as each of these outstanding authors presented their own perspectives on the problems of mathematical communication. -

Magnetic RSA
Magnetic RSA Rémi Géraud-Stewart1;2 and David Naccache2 1 QPSI, Qualcomm Technologies Incorporated, USA [email protected] 2 ÉNS (DI), Information Security Group CNRS, PSL Research University, 75005, Paris, France [email protected] Abstract. In a recent paper Géraud-Stewart and Naccache [GSN21] (GSN) described an non-interactive process allowing a prover P to con- vince a verifier V that a modulus n is the product of two randomly generated primes (p; q) of about the same size. A heuristic argument conjectures that P cannot control p; q to make n easy to factor. GSN’s protocol relies upon elementary number-theoretic properties and can be implemented efficiently using very few operations. This contrasts with state-of-the-art zero-knowledge protocols for RSA modulus proper generation assessment. This paper proposes an alternative process applicable in settings where P co-generates a modulus n “ p1q1p2q2 with a certification authority V. If P honestly cooperates with V, then V will only learn the sub-products n1 “ p1q1 and n2 “ p2q2. A heuristic argument conjectures that at least two of the factors of n are beyond P’s control. This makes n appropriate for cryptographic use provided that at least one party (of P and V) is honest. This heuristic argument calls for further cryptanalysis. 1 Introduction Several cryptographic protocols rely on the assumption that an integer n “ pq is hard to factor. This includes for instance RSA [RSA78], Rabin [Rab79], Paillier [Pai99] or Fiat–Shamir [FS86]. One way to ascertain that n is such a product is to generate it oneself; however, this becomes a concern when n is provided by a third-party.